ISG report claims that moving to cloud operations saves companies an average of 38%1
As a mid-market business leader, one of the most important decisions you make is your approach to digital transformation. A critical part of any digital transformation strategy is the use of cloud technology; particularly cloud communications and collaboration. New cloud delivery of advanced, cognitive collaboration technologies offers the freedom to provide a first-class service experience to customers anywhere on the planet, with rapid, low risk deployment, low up-front costs, and a tightly integrated cloud application workflow model. This can mean the difference between being the agent of change in your industry and watching the market pass you by.
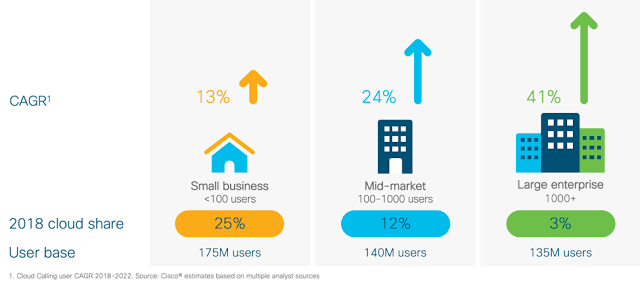
Globally, the mid-market cloud PBX segment is just starting to pick up momentum, with analysts projecting a 24% global segment CAGR of 24% through 2022, to build on a low current market penetration level estimated at 12%. See Figure 1.
Figure 1 – Cloud Calling Market Penetration and Growth Rates by Segment
As a mid-market business leader, one of the most important decisions you make is your approach to digital transformation. A critical part of any digital transformation strategy is the use of cloud technology; particularly cloud communications and collaboration. New cloud delivery of advanced, cognitive collaboration technologies offers the freedom to provide a first-class service experience to customers anywhere on the planet, with rapid, low risk deployment, low up-front costs, and a tightly integrated cloud application workflow model. This can mean the difference between being the agent of change in your industry and watching the market pass you by.
The State of the Cloud Calling Market
Globally, the mid-market cloud PBX segment is just starting to pick up momentum, with analysts projecting a 24% global segment CAGR of 24% through 2022, to build on a low current market penetration level estimated at 12%. See Figure 1.
Figure 1 – Cloud Calling Market Penetration and Growth Rates by Segment
New cloud options, like Cisco Webex Calling, are adding the scalability, reliability and security, along with a more sophisticated collaboration feature set that mid-market business requires. The cloud is better able to economically address the multi-site, contact center and mobile connectivity shortcomings of the on-premises options available to mid-market organizations. Equally important is the ability to support a cloud migration strategy that offers seamless operation throughout the time a business requires use of a mixed cloud/on-premises model. Because most mid-market businesses are not ready to go all-in on the cloud in one step, support for a common dial plan, administration and directory model through this transition period is an essential check point to starting a successful cloud migration.
The Performance Gap Between Leaders and Laggards
The urgency for business to take action now comes down to the performance gap between digital transformation leaders and laggards. Digital transformation can dramatically lower costs, enhance agility and enables mid-market organizations to implement technologies and tools that were once only available to large enterprises. Well executed, these strategies are game changers for the mid-market organization. A Harvard Business School study2 published by Professors Marco Iansiti and Karim Lakhani demonstrated the gap between the top 25% “Digital Leaders” and the bottom 25% “Digital Laggards.” Figure 2 shows a gross margin difference of 18% between the leaders and laggards, and concludes, “Digital Transformation has become the new normal.”
Figure 2 – The digital divide between digital leaders and laggards
Five reasons to implement digital collaboration transformation strategies (Figure 3)
1. Gain large enterprise capabilities without the cost and complexity– Historically, mid-market organizations have been at a disadvantage to larger organizations, due to the high capital cost of implementing sophisticated, complex and expensive IT applications, technologies and infrastructures. Cloud calling, collaboration and contact centers change all these by making advanced tools affordable to the mid-market for the first time.
2. Enhance business agility and reduce operational cost and complexity– Cloud calling, and collaboration allows organizations to seamlessly scale users and sites up or down quickly and predictably, with one global solution that can be centrally managed. Precious capital investments are preserved for more strategic business initiatives while operating budgets become more transparent and predictable, without the headaches of managing surprise PBX upgrades and maintenance. And both management and workforce productivity are vastly improved through the use of always-current and accessible cloud collaboration services.
3. Increase workforce mobility, productivity and satisfaction – A key issue for today’s multi-site enterprise and mobile workforce is the complexity and expense in deploying, managing, keeping up-to-date and networking multiple on-premises systems that typically range from new to decades old. Millennial and Gen Z employees expect advanced collaboration tools in the workplace – the same tools that they use in their private lives – and these have a dramatic impact in both recruitment and retention. They expect a seamless, global and feature rich collaboration experience across any device, network or channel –calling, messaging, team collaboration, video, etc.
4. Strengthen customer journeys and relationships– Most mid-market enterprises must deliver an omni-channel – voice, chat, video, IVR, natural language, bot – customer support experience in their contact centers, inbound/outbound sales and service operations. For many businesses, these solutions are mission critical to their customer relationships and business success. Prior to the cloud, sophisticated contact center solutions that went beyond basic routing and reporting were very expensive and difficult to manage and keep current. The cloud makes the most advanced contact center technologies accessible for businesses of all sizes without the capital investment and operational complexity.
5. Improve business performance and competitiveness– As the Harvard Business School study demonstrates, organization’s financial performance and business outcomes are vastly improved through strategic digital transformation. Successful transformation projects focus on cost reductions, process improvements, adding organizational agility to respond rapidly to changing environments, and one-to-one, team and customer collaboration.
Up until now, the mid-market segment has been slower to implement cloud collaboration transformation strategies, due to the complexity of their transformation journeys and the lack of maturity in cloud solutions. That limit no longer exists. Webex Calling now allows mid-market customers to replace their PBXs and deploy cloud calling and collaboration with confidence, with a proven enterprise platform that is already serving 29 million business users worldwide. Are you ready to take the next step?
Talk to Cisco.
Figure 3 – Five reasons mid-market organizations must implement cognitive collaboration transformations