Embarking on the journey to earn a Cisco certification can be both challenging and rewarding. For those aiming to conquer the 300-715 SISE exam, understanding what resources truly make a difference is paramount. This specialized exam, focused on Implementing and Configuring Cisco Identity Services Engine, is a critical step for security professionals looking to validate their expertise. Success rates often hinge on the quality and strategic utilization of study materials.
It's no secret that a significant majority of individuals who successfully pass the Cisco 300-715 SISE exam don't just 'wing it.' They meticulously plan their preparation, leveraging a curated selection of resources designed to cover every aspect of the exam syllabus. In fact, our research indicates that 90% of 300-715 SISE achievers consistently turn to a specific set of tools and methodologies. This long-form guide is your ultimate companion, meticulously detailing the best study guides, courses, practice tests, and practical advice to help you join the ranks of successful Cisco 300-715 SISE professionals.
Understanding the Cisco 300-715 SISE Exam
Before diving into the resources, it's essential to grasp the core of the Cisco 300-715 SISE exam. This certification validates your skills in implementing and configuring Cisco Identity Services Engine (ISE), a critical component in modern network security strategies. It's a key requirement for the Cisco CCNP Security SISE exam, positioning you as an expert in securing networks with identity-based access control.
Exam at a Glance: 300-715 Implementing and Configuring Cisco Identity Services Engine
- Exam Name: Implementing and Configuring Cisco Identity Services Engine
- Exam Code: 300-715 SISE
- Exam Price: $300 USD
- Duration: 90 minutes
- Number of Questions: 55-65
- Passing Score: Variable (Typically 750-850 out of 1000 Approx.)
This exam is designed for network security engineers, administrators, and system engineers who are responsible for the design, implementation, and management of Cisco Identity Services Engine solutions. Achieving this certification demonstrates a deep understanding of Cisco's security technologies and their practical application.
Benefits of Cisco 300-715 SISE Certification
Earning the Cisco 300-715 SISE certification opens doors to numerous professional advantages. It validates your expertise in a highly sought-after area of network security, making you a valuable asset to any organization. The benefits include enhanced career opportunities, higher earning potential, and recognition as a certified professional capable of implementing robust identity and access management solutions using Cisco ISE. It directly contributes to the prestigious Cisco CCNP Security certification, further solidifying your professional standing.
Deep Dive into the 300-715 SISE Exam Syllabus
A thorough understanding of the Cisco 300-715 SISE exam syllabus is the cornerstone of effective preparation. The exam content is structured around seven key domains, each contributing a specific percentage to the overall score. You can find the detailed 300-715 SISE exam topics on the Cisco Learning Network. Let's break down each domain:
Architecture and Deployment - 10%
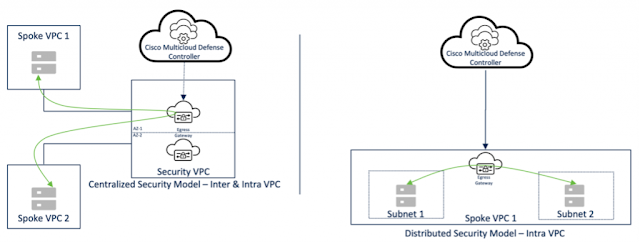
This section focuses on the foundational aspects of Cisco ISE, including its various deployment options, personas (Administration, Policy Service, Monitoring), and how to scale an ISE deployment. Candidates must understand different deployment models, high availability strategies, and hardware/software requirements. Knowledge of distributed deployments, sizing guidelines, and licensing models is also crucial here. Mastering this domain sets the stage for efficient implementation.
Policy Enforcement - 25%
Representing the largest portion of the exam, policy enforcement is central to What is Cisco Identity Services Engine. This domain covers the configuration of authentication and authorization policies, including MAB, 802.1X, and other access control methods. You'll need to know how to create policy sets, implement authentication rules using various identity sources (Active Directory, internal users), and define authorization policies based on user groups, device types, and network conditions. Practical skills in applying DACLs, named ACLs, and Security Group Tags (SGTs) are critical for securing network access.
Web Auth and Guest Services - 15%
Managing guest access and providing secure web authentication are vital functions of Cisco ISE. This section delves into configuring guest access policies, including sponsored and self-registered guest portals. It covers various web authentication flows, custom portal creation, and integrating with external identity sources for guest accounts. Understanding the visitor management lifecycle and troubleshooting common guest access issues will be key to excelling in this area.
Profiler - 15%
The Profiler domain emphasizes the ability to identify and classify devices connecting to the network. This involves configuring profiling probes (SNMP, DHCP, DNS, HTTP), creating custom profiling policies, and leveraging profiling data for authorization decisions. Candidates should be proficient in using profiling to enhance visibility, enforce context-aware policies, and ensure proper device segmentation within the network.
BYOD - 15%
Bring Your Own Device (BYOD) is a pervasive challenge, and Cisco ISE provides robust solutions. This domain covers the implementation of BYOD policies, including device registration, on-boarding flows (single SSID, dual SSID), and certificate provisioning using internal or external CAs. You'll need to understand how to configure supplicant provisioning, create device registration portals, and enforce policies tailored to personal devices.
Endpoint Compliance - 10%
Ensuring endpoint compliance is crucial for maintaining a secure network posture. This section focuses on configuring client-side posture assessment using Cisco AnyConnect. It involves defining posture requirements, creating compliance policies, and understanding the remediation process for non-compliant devices. Knowledge of different compliance modules and their deployment is essential.
Network Access Device Administration - 10%
This domain covers the administration of network devices using TACACS+. Candidates will need to configure TACACS+ policy sets, command sets, and shell profiles to control administrative access to network devices. Understanding how to integrate network devices with ISE for centralized authentication, authorization, and accounting (AAA) of administrative users is a core skill tested here. This also involves securing access to various network devices such as routers, switches, and firewalls using Cisco ISE.
Core Resources for 300-715 SISE Success
Now that we've outlined the exam content, let's explore the essential resources that 90% of successful candidates utilize for their Cisco 300-715 SISE preparation. Combining these elements provides the best Cisco 300-715 SISE preparation strategy.
1. Official Cisco Study Resources
When it comes to preparing for any Cisco certification, the official resources from the vendor are always the first and most authoritative stop.
- Cisco Learning Network: This is an invaluable online community and resource hub where you can find detailed official exam details, study groups, forums, and additional learning materials directly from Cisco. It's a great place to clarify doubts and interact with fellow learners and Cisco experts.
- Official Cisco Training Courses: Cisco offers an official training course specifically designed for this exam. The "Implementing and Configuring Cisco Identity Services Engine (SISE) v3.0" course provides structured learning, hands-on labs, and expert instruction covering the entire Cisco 300-715 SISE course content. This formal training is often the bedrock of many successful preparation journeys.
- Cisco Documentation: For a deep dive into specific features and configurations, the official Cisco documentation is unmatched. Referencing the Cisco ISE implementation guide and various configuration guides for Configuring Cisco Identity Services Engine provides granular details that are critical for complex topics. This is especially useful for understanding the nuances of implementation.
2. High-Quality Study Guides and Books
While official courses provide a structured path, dedicated study guides and books offer comprehensive textual explanations and often come with review questions and practical exercises.
- Official Cert Guides: Look for official certification guides from Cisco Press or other reputable publishers. A well-written Cisco 300-715 SISE study guide will systematically cover each syllabus topic, providing in-depth explanations, configuration examples, and scenarios relevant to the exam. These guides are often reviewed by subject matter experts, ensuring accuracy and relevance.
- Complementary Technical Books: Beyond certification-specific guides, consider books that focus purely on Cisco Identity Services Engine (SISE) implementation and advanced configurations. These can offer a broader perspective and deeper understanding of the technology, which is beneficial for tackling complex exam questions and real-world scenarios.
3. Practice Tests and Exam Simulators
Simulating the exam experience is critical for success. Practice tests help you identify knowledge gaps, manage your time effectively, and get comfortable with the exam format. Many successful candidates attest to the power of dedicated practice before the actual exam.
- Realistic Practice Exams: Seek out high-quality Implementing and Configuring Cisco Identity Services Engine practice test platforms. These should offer a realistic exam environment, including timed sections and a variety of question types. Focusing on a reliable 300-715 SISE practice test can help gauge your readiness and build confidence.
- Cisco 300-715 SISE Exam Questions: Regularly testing yourself with a diverse set of Cisco 300-715 SISE exam questions is vital. This helps reinforce learning and exposes you to different ways topics might be presented in the exam. While some candidates might look into 300-715 SISE dumps, it's crucial to use them judiciously. Pure memorization of dumps often leads to failure, as exam questions are frequently updated and test understanding, not rote recall. Instead, use practice questions to test your comprehension and identify areas needing more study.
4. Online Courses and Video Training
For many visual learners or those who prefer a guided approach, online courses offer an excellent alternative or supplement to traditional books.
- Video Lecture Series: Platforms like Udemy, Pluralsight, INE, or CBT Nuggets often host comprehensive video courses taught by industry experts. These courses can break down complex topics into digestible modules, providing demonstrations and real-world examples that enhance understanding of the Cisco 300-715 SISE exam content.
- Live Online Bootcamps: Some training providers offer live online bootcamps that combine instructor-led sessions with interactive labs. These can be particularly effective for individuals who thrive in a structured, real-time learning environment and want to quickly grasp the nuances of Configuring Cisco Identity Services Engine.
5. Hands-on Lab Experience
Theory is important, but practical experience is indispensable for the 300-715 SISE exam. Cisco ISE is a hands-on technology, and the exam expects you to demonstrate implementation and configuration skills.
- Building a Lab Environment: Setting up your own virtual lab using VMware Workstation or EVE-NG with Cisco ISE virtual appliances is highly recommended. This allows you to practice all configurations covered in the syllabus, from basic deployments to complex policy enforcements, BYOD, and profiling.
- Cisco Modeling Labs (CML) / DevNet Sandbox: Cisco offers official lab environments and sandboxes where you can get hands-on experience with ISE without needing to build your own infrastructure. These resources are excellent for experimenting with different configurations and troubleshooting scenarios. Regularly performing configurations in a lab environment is arguably the most critical step for passing.
Strategies for Mastering the 300-715 SISE Exam
Beyond resources, your study strategy plays a pivotal role in how to pass Cisco 300-715 SISE.
- Create a Detailed Study Plan: Break down the Cisco 300-715 SISE exam syllabus into manageable chunks. Allocate specific time slots for each domain, giving more attention to areas where you feel weaker or those with higher exam weight (e.g., Policy Enforcement). Consistent study over several weeks or months is far more effective than cramming.
- Focus on Concepts AND Configuration: The exam will test both your theoretical understanding and your practical ability to configure Cisco ISE. Don't just read about it; configure it repeatedly in your lab. Understand the 'why' behind each command and policy.
- Master Time Management: With 55-65 questions in 90 minutes, time is of the essence. Practice tests help you improve your pace. Learn to quickly identify question types and manage your time per question.
- Review and Re-evaluate: After taking practice tests, don't just look at the score. Analyze incorrect answers to understand *why* you got them wrong. Revisit the relevant study material and lab configurations. This iterative process of study, practice, and review is fundamental.
- Understand the Passing Score: While the Cisco 300-715 SISE pass score is variable, typically around 750-850 out of 1000, aim much higher in your practice tests (e.g., 900+) to build a buffer and confidence for the actual exam.
- Leverage the Community: Engage with online forums, study groups, and social media groups dedicated to Cisco certifications. Asking questions, sharing insights, and learning from others' experiences can provide valuable perspectives and keep you motivated. You can find more comprehensive certification insights and study tips on Cisco Central Blog.
Conclusion
Achieving the Cisco 300-715 SISE certification is a testament to your expertise in securing modern networks with Cisco Identity Services Engine. It's a challenging but highly rewarding endeavor that requires dedication, the right resources, and a strategic approach. By integrating official Cisco resources, high-quality study guides, realistic practice tests, online courses, and crucial hands-on lab experience, you align yourself with the 90% of achievers who have successfully navigated this exam.
Remember, the journey to certification is a marathon, not a sprint. Arm yourself with these proven resources, commit to a consistent study plan, and continuously reinforce your knowledge with practical application. Your dedication today will unlock significant professional opportunities tomorrow.
Start your comprehensive Cisco 300-715 SISE preparation today and take a definitive step towards advancing your career in network security!
Frequently Asked Questions (FAQs)
1. What is the Cisco 300-715 SISE exam?
The Cisco 300-715 SISE exam, officially titled "Implementing and Configuring Cisco Identity Services Engine," is a certification exam that validates a candidate's skills in deploying, configuring, and managing Cisco ISE solutions for network access control, guest services, BYOD, and compliance. It is a core exam for the CCNP Security certification.
2. How much does the Cisco 300-715 SISE certification cost?
The standard Cisco Identity Services Engine (SISE) certification cost for the 300-715 SISE exam is $300 USD. This price may vary slightly based on regional taxes or currency exchange rates.
3. What are the key topics covered in the 300-715 SISE exam?
The exam covers seven main domains: Architecture and Deployment, Policy Enforcement, Web Auth and Guest Services, Profiler, BYOD, Endpoint Compliance, and Network Access Device Administration. Policy Enforcement carries the highest weight at 25%.
4. How important is hands-on experience for this exam?
Hands-on experience is critically important for the 300-715 SISE exam. Cisco ISE is a practical technology, and the exam tests your ability to implement and configure it. Practical lab work, whether through building your own virtual lab or using Cisco's official labs, is essential for truly understanding the concepts and passing the exam.
5. Are 300-715 SISE dumps recommended for preparation?
While some candidates may encounter 300-715 SISE dumps, relying solely on them for memorization is not recommended. Cisco frequently updates its exams, and dumps often contain outdated or incorrect information. The best approach is to use high-quality practice tests to gauge your knowledge and identify weak areas, focusing on a deep understanding of the concepts rather than rote memorization of questions and answers.