Today marks an important milestone for Cisco’s Data Center offerings to our customers with the unveiling of a new ACI technology ecosystem partner solution. We are pleased to announce availability of “AlgoSec Security Management Solution” on Cisco’s Global Price List.
“AlgoSec Security Management solution (ASMS)” has delivered tremendous value to our joint customers across the world, with its ability to extend ACI’s policy-driven automation to security devices in the fabric, helping them automate policy enforcement for security devices in the fabric and ensure continuous compliance across multicloud ACI environments. To make it easier for our customers to procure that solution, we onboarded AlgoSec to Cisco Global Price List through Cisco DevNet Solutions Plus Program. Now Cisco’s direct and channel sales network can offer AlgoSec’s solution together with Cisco networking products as a single package. For details on AlgoSec solution orderability, check Cisco commerce.
What makes this solution compelling for you as a Cisco customer or a partner? Rapidly changing business needs and application connectivity requirements in modern data centers pose big challenges to ensuring compliance and security. With thousands of firewall rules across many different security devices, frequent changes, limited visibility and lack of trained security personnel , managing security policies manually is now impossible. This is where ASMS (AlgoSec Security Management Solution) comes in.
ASMS automates and orchestrates network security policy management, maps and migrate application connectivity, and proactively analyze risk to applications risk – across any cloud and on-premise networks.
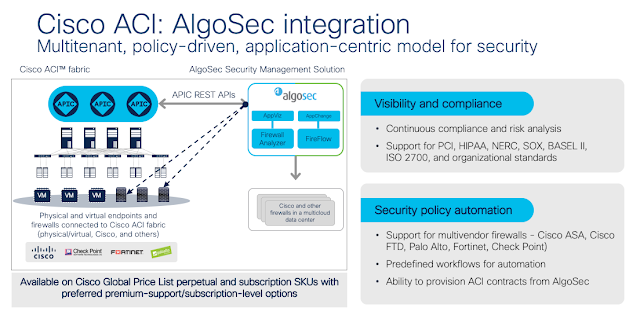
AlgoSec integrates with Cisco ACI to extend ACI’s Application centric policy- based automation to AlgoSec managed security devices across their data center, on its edges and in the cloud. AlgoSec Security Management Solution for ACI enables customers to ensure continuous compliance and automate the provisioning of security policies not just across the ACI fabric but also across multi-vendor security devices connected to ACI fabric, helping customers build secure data centers. The solution is based on Cisco APIC and ASMS integration to deliver a powerful multi-tenant, policy-driven, application-centric model for network security. Read Solution brief for details.
The AlgoSec Security Management Solution comprises three key components – AlgoSec Firewall Analyzer, AlgoSec Fireflow, and AlgoSec Application Connectivity Management.
What makes this solution compelling for you as a Cisco customer or a partner? Rapidly changing business needs and application connectivity requirements in modern data centers pose big challenges to ensuring compliance and security. With thousands of firewall rules across many different security devices, frequent changes, limited visibility and lack of trained security personnel , managing security policies manually is now impossible. This is where ASMS (AlgoSec Security Management Solution) comes in.
ASMS automates and orchestrates network security policy management, maps and migrate application connectivity, and proactively analyze risk to applications risk – across any cloud and on-premise networks.
AlgoSec integrates with Cisco ACI to extend ACI’s Application centric policy- based automation to AlgoSec managed security devices across their data center, on its edges and in the cloud. AlgoSec Security Management Solution for ACI enables customers to ensure continuous compliance and automate the provisioning of security policies not just across the ACI fabric but also across multi-vendor security devices connected to ACI fabric, helping customers build secure data centers. The solution is based on Cisco APIC and ASMS integration to deliver a powerful multi-tenant, policy-driven, application-centric model for network security. Read Solution brief for details.
The AlgoSec Security Management Solution comprises three key components – AlgoSec Firewall Analyzer, AlgoSec Fireflow, and AlgoSec Application Connectivity Management.
AlgoSec Firewall Analyzer (AFA) – Network Security Policy Analysis, auditing and compliance
AlgoSec Firewall Analyzer delivers visibility and analysis of complex network security policies across Cisco ACI, firewalls attached to ACI fabric and other upstream security devices. The solution automates and simplifies security operations including troubleshooting, auditing policy cleanup, risk and compliance analysis and audit preparations.
AlgoSec FireFlow (AFF) – Security Policy Change Automation
AlgoSec FireFlow helps you process security policy changes in a fraction of the time, so you can respond to business requirements with the agility they demand. FireFlow automates the entire security policy change process — from design and submission to proactive risk analysis, implementation, validation and auditing with the support for automated policy enforcement on Cisco ACI and multi-vendor security devices, including Cisco ASA & FTD, Check Point Software, Fortinet and Palo Alto Networks.
AlgoSec Application Connectivity Management: AlgoSec AppViz & AppChange
The AppViz (Application Visibility Add-On) add-on accelerates identification and mapping of all the network attributes and rules that support business-critical applications – making it easier for organizations to make changes to their applications across any on-premise and cloud platform, and to troubleshoot network and change management issues across the entire enterprise environment.
AlgoSec’s AppChange (Application Lifecycle Change Management Add-On) automatically translates and implements network security policy changes on all relevant devices across the entire network to reflect specific connectivity requirement for applications. This saves time for IT and security teams and eliminates manual errors and misconfigurations. AppChange addresses the critical issues of human error and configuration mistakes that are the biggest causes of network and application outages.
These components are offered as independent software licenses and bundles on Cisco’s Global Price List.
In summary, the AlgoSec Security Management Solution integrates with and complements Cisco ACI Anywhere, providing consistent security policy management and visibility across data centers and clouds.