To protect business critical data, the network needs to be segmented. But traditional methods are complex. Cisco TrustSec provides a simple way to segment and apply polices uniformly across the network.
Traditional network segmentation approaches use IP address-based access control lists (ACLs), VLAN segmentation, and firewall policies that require extensive manual maintenance. Therefore, every device in the network that needs to enforce security policies would require manual configuration. For instance, any change to policies would mean manually updating the ACLs for all the devices uniformly which is error prone. With IOT and BYOD the scale factor will make it very difficult to use traditional ACLs.
Having a single centralized security policy database would be easy to maintain and policies can be uniformly enforced. This is where trustSec becomes relevant. TrustSec provides an end-to-end secure network where each entity is authenticated and trusted by its neighbors. Above all, it provides consistent policy set across the network.
This blog provides an overview of how trustSec as a solution is deployed on 9800 and 8540 Wireless LAN Controller. In addition, some key feature differentiators is also highlighted.
Terminology
Security Group
Used for grouping users and endpoints that should have a similar access control policy.
Security Group Tag (SGT)
It is a unique security group number that gets assigned to the security group.
TrustSec Capable Device
Devices that are capable of understanding SGT (hardware or software based).
Protected Access Credential (PAC)
Shared credential used to mutually authenticate Trustsec capable devices with ISE.
Environment (Env) Data
ISE provides ENV data information to a trustSec capable device. It consist of : Server list, expiry/refresh timeout and device SGT.
◉ Server list – It provides the list of radius servers which can be used for authentication and authorization.
◉ Expiry/Refresh timeout – Configurable timer on ISE which will let the administrator know how often the device should refresh the environment data.
◉ Device SGT – This is the SGT assignment for the device.
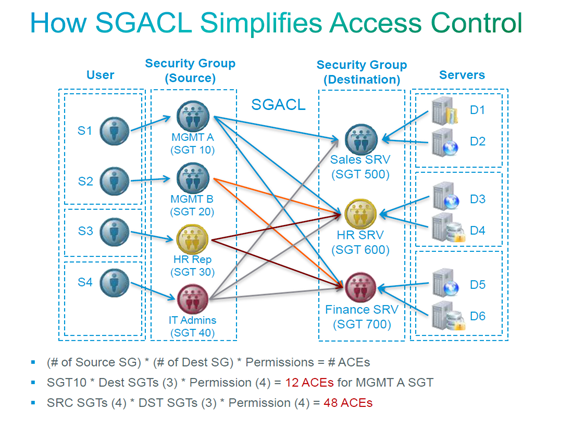
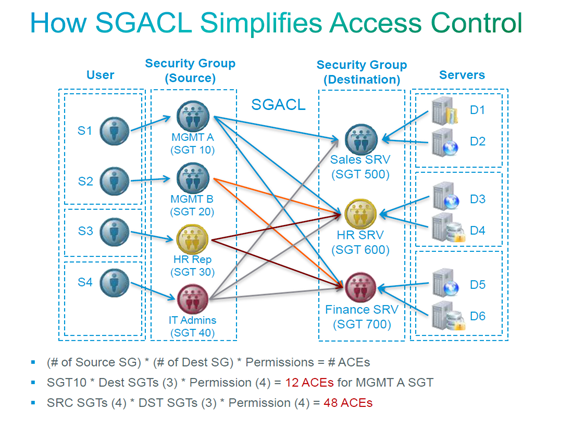
Security Group Access Control List (SGACL)
Access and permission are provided based on the SGT information.
With increase in number of source and destination the ACL size could grow exponentially making it difficult to maintain. In other words, it takes a lot of effort for an administrator to manually update ACL across network devices. For example, here is a pictorial representation of how trustSec as a solution can make things easy for an administrator.

Key components
There are three components within TrustSec domain.
1. Classification: Client classification at ingress by centralized policy database (ISE) and assigning unique S-SGT to client based on client identity attributes.
2. Propagation: Propagation of IP to SGT binding to neighboring devices using SXPv4 or inline tagging.
3. Enforcement: SGACL download at enforcement point for (S-SGT, D-SGT) and enforcing the policy.
Given below are some details about trustSec implementation on 8540 and 9800 Wireless LAN controllers.
Classification
It happens on ISE at the ingress and the clients get the SGT based on client identity attributes. So, the ISE acts as the central policy manager providing SGT for the clients.
Propagation and Enforcement
There are two modes for SGT propagation:
SXPv4
SXP is a control protocol which propagates IP address to Security Group Tag (SGT) binding information across network devices. Using the SGT and SGACL information, the endpoint device(WLC or AP) can enforce traffic.
8540 Central switching
The controller can act ONLY as a speaker. This means that the SGT information of the wireless client is propagated to the enforcement point by the controller. But enforcement happens at the AP for the traffic towards the client.
9800 Central switching
The controller can act as Listener, Speaker and both mode. In listener mode, controller can enforce traffic. Whereas controller in both mode can enforce and as well as propagate SGT information to the enforcement point.
An important difference between 8540 and 9800 controller in central switching deployment – On 8540, the enforcement happens on the AP. Whereas, on 9800 enforcement happens on the WLC.
Local switching
The Access point acts as Listener, Speaker and both modes. In listener mode, the access point can enforce traffic. On the other hand, access point in both mode can enforce and propagate SGT information to the enforcement point. This functionality is common between 8540 and 9800 deployments.
Inline tagging
Inline tagging involves tagging each packet egressing the controller by inserting a CMD header.
For inbound packets (towards client), the CMD header is stripped if present. The client S-SGT is used to find SGACL associated with (S-SGT, D-SGT) for enforcement.
8540 Central switching
WLC performs inline tagging for all packets sourced from wireless clients that reside on the WLC by tagging it with Cisco Meta Data (CMD) tag. For packets inbound (towards client), WLC strips the packet of the CMD header and pushes the SGT information to the AP for enforcement. Note that the enforcement doesn’t happen on WLC.
9800 Central switching
The WLC performs inline tagging for all packets sourced from wireless clients. For the inbound traffic (towards client), WLC strips the CMD and learns the SGT information from the meta data header. WLC will enforce the traffic using the SGT information.
Local switching
AP performs inline tagging for all packets sourced from wireless clients that reside on the AP by tagging it with Cisco Meta Data (CMD) tag. On the other hand, for packets inbound (towards client) AP will strip the CMD header and act as an enforcement point. This functionally is common between 8540 and 9800 deployments.
In a nutshell, propagation and enforcement happens on the WLC or AP depending on the deployment method (Central and Flex local switching) and the type of controller (9800 or 8540) deployed in the network.
TrustSec – Key feature comparison

Source: cisco.com