At the edge, where new data is generated. In the cloud, any cloud, or on-premise, where it’s processed. Wherever it makes the most sense to execute at speed. Ready and able to provide intelligence on the spot. Ready for change. Ready for growth.
Modern IT infrastructure is performing an intricate and elaborate dance with these data sources and requirements. Cisco’s ACI Anywhere is that critical infrastructure component enabling policy driven network automation for connectivity and segmentation for these data elements, independent of where data resides.
Cisco ACI Anywhere now delivers a true hybrid multicloud capability for customers, taking a holistic, policy driven abstraction on top of cloud native APIs , regardless of the type of workload – physical, virtual, or containerized, across on-premises and/or public cloud.
Cloud Challenges
During recent conversations with customers who operate some of the most demanding and complex data center environments, we found that many are dealing with the same issues, such as:
◈ Inconsistent segmentation capabilities across hybrid instances pose security, compliance, and governance challenges
◈ Complex operational models due to diverse and disjointed visibility and troubleshooting capabilities, with no correlation across different cloud service providers. .
◈ Managing secure connectivity across these hybrid data and application workload environments.
◈ Multiple panes needed to configure, manage, monitor, and operate these multicloud instances.
◈ Last, but not least, training and learning new cloud native constructs.
Solving the Challenges
As the premier policy-driven infrastructure solution for the largest enterprises, Cisco ACI can play a key role in enabling customers to embrace multicloud capabilities.
Cisco Cloud Application Centric Infrastructure (Cloud ACI) is a comprehensive solution for automated network connectivity, consistent policy management, and simplified operations for multicloud environments.
The solution captures business and user intent, uses group-based network and security policy models, and translates them into cloud-native policy constructs for applications deployed across various cloud environments.
Cloud ACI Solution Core Components
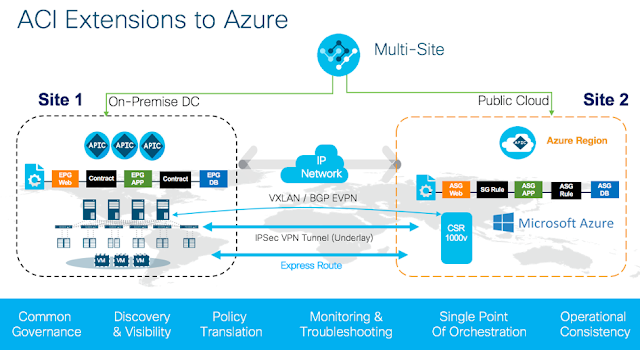
While customers benefit from an ACI policy driven infrastructure in the on-premises environment, Cisco Cloud ACI allows them to automate the management of end-to-end connectivity, as well as the agentless enforcement of consistent security policies, for workloads across on-premises and in public clouds through a single pane of glass.
Key components include:
◈ Multisite Orchestrator (hosted anywhere) for inter-site policy definition
◈ Cisco’s Cloud Application Policy Infrastructure Controller (APIC) runs natively in public clouds to provide automated connectivity, policy translation, day two operations, and enhanced visibility of workloads in the public cloud
◈ CSR 1000V instance (runs in the cloud) for IPSec VPN tunnel (Underlay), and VXLAN (overlay termination) for data-plane connectivity between on-premises and cloud
Accelerating Cloud-based Journeys – What’s New?
For customers whose journeys start in the cloud, we are now introducing the Cloud-first ACI solution, or ACI Multicloud, which uncouples the solution from the on-premises data center and allows you to securely connect and segment workloads not only in the public cloud, but also across public clouds.
For customers extending their on-premises ACI infrastructure into public cloud, we are now introducing Cloud ACI extensions to Azure cloud, in addition to the already shipping Cloud ACI extensions on AWS.
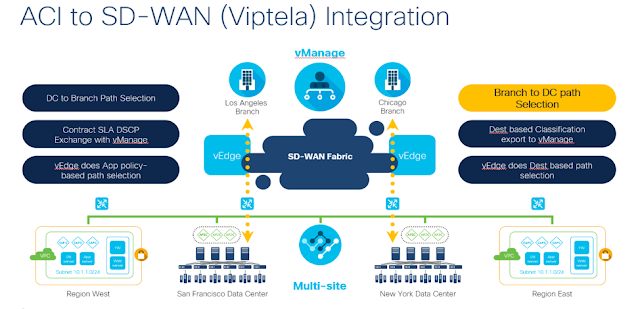
We are also introducing new ACI and SDWAN integration for branch offices (Network Edge). An integral component of customers cloud journey also requires secure, policy driven interconnects between the data center and branch offices, that are a cost-efficient alternative to provisioning dedicated connections. Through this integration, customers can now automate WAN path selection between the branch office and the on-premises data center based on application policy.
Enjoy the benefits of a policy driven infrastructure … Anywhere
Collectively, these capabilities reduce management complexity, enable a common governance and security posture, simplify ‘Day 2 operations’ with enhanced visibility across on-premises and public cloud, while leveraging the rich native services available in public clouds for scale and flexibility.
Customers can benefit from secure workload mobility and preserve the application policies, network segmentation, and identity of the workloads, whether it’s to achieve their business continuity, disaster recovery mandates, cloud bursting SLAs, or simply accelerating your cloud migration journey.
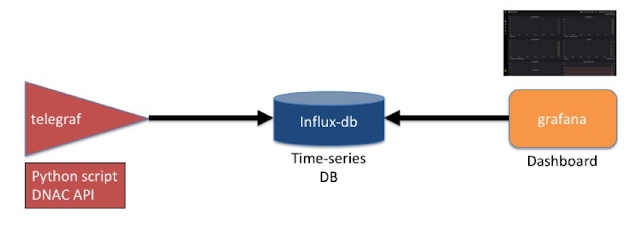
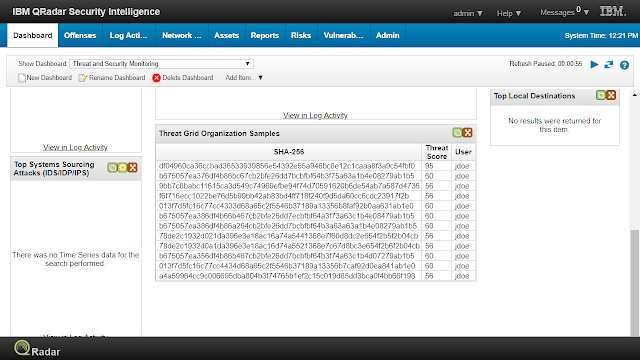
In addition, customers can benefit from Cisco ACI broad ecosystem that allows for integration with most commonly deployed solutions such as Cisco AppDynamics, CloudCenter, F5, Citrix, ServiceNow, Splunk, SevOne, and Datadog.
With new Azure extensions, customers can tap into the rich cross-silo insights through ACI integrations with Azure technologies like Azure Monitor*, Azure Resource Health* and Azure Resource Manager * to fine-tune their network operations for speed, flexibility and cost.
Customers can leverage widely adopted tools such as Terraform and Ansible to achieve end-to-end workflow-based automation.
“ESG Research validates that companies are increasingly adopting a hybrid cloud approach as a centerpiece of the their digital transformation journeys. In fact, many are standardizing on a Multi-cloud policy.
However, these distributed compute environments create significant management and operational complexity. Cisco ACI Anywhere, and more specifically, Cloud ACI for Microsoft Azure with its native integration in Azure, is the “Easy” button that helps to consolidate and simplify management across the on-premises data center and the popular Azure cloud environment.
It enables a common policy ,security and governance framework across all locations enabling consistent application segmentation, access control and isolation across varied deployment models. We expect this message to resonate with all market segments and customers.”
—Bob Laliberte, Practice Director and Senior Analyst with the Enterprise Strategy Group.
Looking Towards the Future
Our ACI anywhere vision is to provide the freedom of choice, agility, security, and flexibility of being able to connect and run your workloads Anywhere without compromising your security and governance mandates.
With the new ‘Cloud ACI on Azure’ and ‘Cloud First ACI’, along with ‘ACI and SD-WAN’ integration, Cisco has taken another huge step forward toward delivering that vision. And there is more to come in future.