We’ve reached an interesting turning point for encrypted traffic.
Gartner predicted that 80% of web traffic would be encrypted by 2019. Sure enough, this prediction came true. Last year, the team at Let’s Encrypt, an organization that helps enable encryption for websites, cited that 80% of web traffic they’ve seen is now encrypted. We have reached the point where the average volume of encrypted traffic on the internet has now surpassed the average volume of unencrypted traffic.
This is largely good news, as moving forward, encrypting internet traffic is now the new norm online and will continue to grow. This is good for data privacy and should let us sleep a bit easier knowing that as out information traverses the internet, it’ll be encrypted.
However, much like the adoption rate of encrypted traffic, encrypted threats are also on the rise. This year, Gartner has predicted that more than 70% of malware campaigns will use some type of encryption to conceal malware delivery, command-and-control activity, or data exfiltration. Complicating matters, it’s also predicted that 60% of organizations will fail to decrypt HTTPS efficiently, thereby missing critical encrypted threats.
Traditional threat inspection methods that rely on bulk decryption, analysis, and re-encryption are not always practical or feasible, for both performance and resource reasons. These methods also compromise privacy and data integrity. Unfortunately, many organizations do not have a way to detect malicious activity in encrypted traffic without the use of decryption. With the growing amount of encrypted traffic and the number of threats hiding within it, how should organizations ensure the encrypted traffic coming into their network is safe, without compromising the integrity of that data?
Stealthwatch Cloud is a Software-as-a-Service (SaaS) solution that is easy to try, easy to buy, and simple to operate and maintain. Stealthwatch Cloud analyzes network behavior to detect advanced threats, even those hiding in encrypted traffic. Cisco’s proprietary Encrypted Traffic Analytics (ETA) technology uses attributes like Initial Data Packet (IDP) to detect malware in encrypted traffic, without decrypting the data.
Recently, Stealthwatch Cloud has added further integrations with Cognitive Intelligence, our amazing cloud-based machine learning and AI R&D team as well as its Confirmed Threat Service.
These integrations allow Stealthwatch Cloud to ingest ETA telemetry from supported Cisco networking devices and provide additional, enhanced fidelity of encrypted (as well as non-encrypted) traffic. From there, ETA will alert users of potential threats that might be hiding in encrypted traffic. These alerts include cryptomining, unpublished TOR, botnets, Ramnit, Sality, malicious file download, phishing and typosquatting and more.
In a performance study by Miercom, Cisco Encrypted Traffic Analytics showed as much as 36% faster rates of detection, finding 100% of threats in three hours. Furthermore, the study found that Cisco ETA detected 100% of malicious flows within three hours
Cognitive Intelligence’s Confirmed Threat Service provides Stealthwatch Cloud with a list of high-confidence Indicators of Compromise (IOCs in the form of IPs and domains), a full description of the related global threat, and a write-up of recommended remediation steps. These IOCs are generated as a result of processing billions of connections from across the globe using a pipeline of analytical techniques which include the collection of Initial Data Packets. In essence, the Confirmed Threat Service is the outcome of multi-layered machine learning and encrypted traffic analytics that can convict known as well as unknown global threat campaigns. Cisco ETA can match field data extracted from the IDP against known IOCs which allows Stealthwatch Cloud to then correlate local customer telemetry to the global Confirmed Threat Service.
Gartner predicted that 80% of web traffic would be encrypted by 2019. Sure enough, this prediction came true. Last year, the team at Let’s Encrypt, an organization that helps enable encryption for websites, cited that 80% of web traffic they’ve seen is now encrypted. We have reached the point where the average volume of encrypted traffic on the internet has now surpassed the average volume of unencrypted traffic.
This is largely good news, as moving forward, encrypting internet traffic is now the new norm online and will continue to grow. This is good for data privacy and should let us sleep a bit easier knowing that as out information traverses the internet, it’ll be encrypted.
However, much like the adoption rate of encrypted traffic, encrypted threats are also on the rise. This year, Gartner has predicted that more than 70% of malware campaigns will use some type of encryption to conceal malware delivery, command-and-control activity, or data exfiltration. Complicating matters, it’s also predicted that 60% of organizations will fail to decrypt HTTPS efficiently, thereby missing critical encrypted threats.
Traditional threat inspection methods that rely on bulk decryption, analysis, and re-encryption are not always practical or feasible, for both performance and resource reasons. These methods also compromise privacy and data integrity. Unfortunately, many organizations do not have a way to detect malicious activity in encrypted traffic without the use of decryption. With the growing amount of encrypted traffic and the number of threats hiding within it, how should organizations ensure the encrypted traffic coming into their network is safe, without compromising the integrity of that data?
A better approach to analyzing encrypted traffic
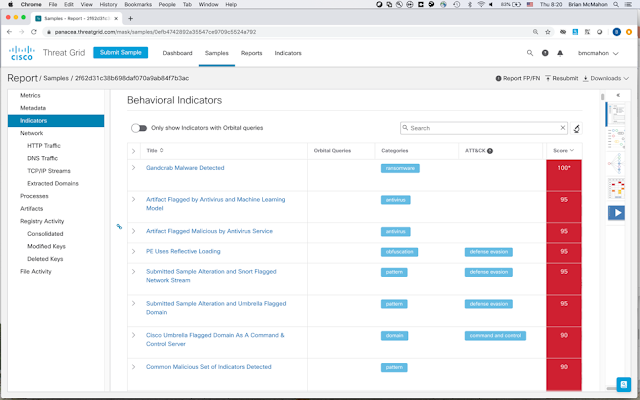
Stealthwatch Cloud is a Software-as-a-Service (SaaS) solution that is easy to try, easy to buy, and simple to operate and maintain. Stealthwatch Cloud analyzes network behavior to detect advanced threats, even those hiding in encrypted traffic. Cisco’s proprietary Encrypted Traffic Analytics (ETA) technology uses attributes like Initial Data Packet (IDP) to detect malware in encrypted traffic, without decrypting the data.
Recently, Stealthwatch Cloud has added further integrations with Cognitive Intelligence, our amazing cloud-based machine learning and AI R&D team as well as its Confirmed Threat Service.
These integrations allow Stealthwatch Cloud to ingest ETA telemetry from supported Cisco networking devices and provide additional, enhanced fidelity of encrypted (as well as non-encrypted) traffic. From there, ETA will alert users of potential threats that might be hiding in encrypted traffic. These alerts include cryptomining, unpublished TOR, botnets, Ramnit, Sality, malicious file download, phishing and typosquatting and more.
In a performance study by Miercom, Cisco Encrypted Traffic Analytics showed as much as 36% faster rates of detection, finding 100% of threats in three hours. Furthermore, the study found that Cisco ETA detected 100% of malicious flows within three hours
How it Works
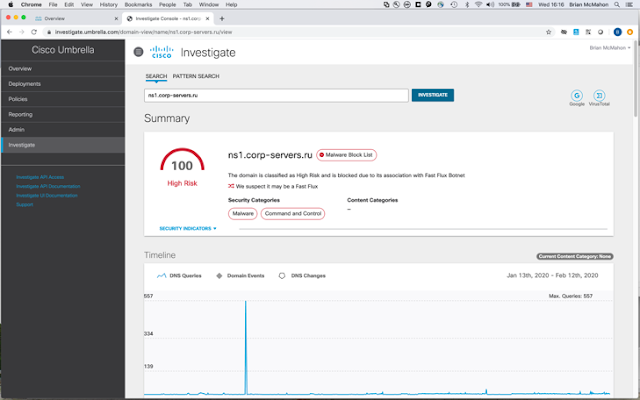
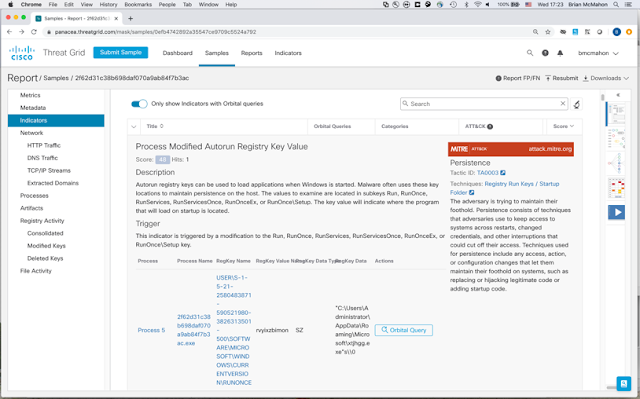
Cognitive Intelligence’s Confirmed Threat Service provides Stealthwatch Cloud with a list of high-confidence Indicators of Compromise (IOCs in the form of IPs and domains), a full description of the related global threat, and a write-up of recommended remediation steps. These IOCs are generated as a result of processing billions of connections from across the globe using a pipeline of analytical techniques which include the collection of Initial Data Packets. In essence, the Confirmed Threat Service is the outcome of multi-layered machine learning and encrypted traffic analytics that can convict known as well as unknown global threat campaigns. Cisco ETA can match field data extracted from the IDP against known IOCs which allows Stealthwatch Cloud to then correlate local customer telemetry to the global Confirmed Threat Service.
New alerts created via this threat intelligence will show up as “Confirmed Threat Watchlist Hit” alerts. These alerts can include named malware type families and also provide details on what they do (exfiltration, exploit, content distribution, botnets, ransomware, etc). Some of the threat intelligence provided by the Confirmed Threat Service is created in collaboration with Cisco Talos. Talos will seed intelligence (initial set of seed IOCs), title and description of a threat. Cognitive Intelligence will then expand this seed set of IOCs with new occurrences using information gathered from IDPs and machine learning – which in turn yields new IPs and domains that are also related to the given threat and appear in real customer telemetry.
Meeting Compliance Needs
In addition to being able to effectively monitor encrypted traffic coming into their network, organizations also have to consider how they use encryption on their own data. When using encryption for data privacy and protection, an organization should be able to answer major questions:
How much of the digital business uses strong encryption?
What is the quality of that encryption?
This information is critical to prevent threat actors from getting into the encrypted stream in the first place. Today, the only way to ensure that encrypted traffic is policy compliant is to perform periodic audits to look for any TLS violations. However, this method isn’t perfect due to the sheer number of devices and the amount of traffic flowing through most businesses.
Cisco Encrypted Traffic Analytics provides continuous monitoring without the cost and time overhead of decryption-based monitoring. Using the collected enhanced telemetry, Stealthwatch provides the ability to view and search on parameters such as encryption key exchange, encryption algorithm, key length, TLS/SSL version, etc. to help ensure cryptographic compliance.
Together, Cisco ETA and Stealthwatch Cloud can also identify encryption quality instantly from every network conversation, providing organizations with the visibility to ensure enterprise compliance with cryptographic protocols. These tools deliver the knowledge of what is being encrypted and what is not being encrypted on your network so you can confidently claim that your digital business is protected and compliant. This cryptographic assessment is displayed in Stealthwatch Cloud and can be exported via APIs to third-party tools for monitoring and auditing of encryption compliance.