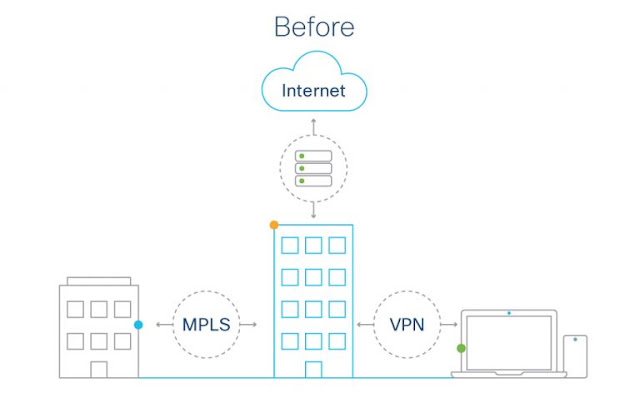
Over the last 20 years of enterprise computing, we’ve seen big changes in work environments and IT setups.
At the turn of the millennium, most employees worked at headquarters or in a branch office, and most software ran from on-site servers. Networks were designed with centralized architecture, with all traffic being routed through the corporate data center over MPLS or VPN. As a result, the entire security stack could be deployed on-premises in a single place.
Let’s delve into the specifics of these two use cases and the SASE and SD-WAN benefits for each.
Use case 1: Secure remote workers
Protecting employees, customers, and other users from cyber threats while providing seamless connectivity is challenging on several fronts:
◉ Enforcing safe access: Provisioning remote workers and connecting branches at scale creates a lot of complexity across IT, security, and networking teams. The demand for broader access also intensifies security threat vectors. Since employees need secure access everywhere, security services must be everywhere too. But it’s difficult to verify users’ identities and the health of their devices, and security policies aren’t consistently applied across environments. In addition, users are left unprotected when they decide to bypass the VPN and on-prem security stack.
◉ Keeping up with evolving threats: Gaps in protection are hard to pinpoint and fix consistently. Responses take more time when stronger integrations across the security stack are lacking.
◉ Maintaining performance: When remote environments and connectivity aren’t under organizational control, it can be hard to pinpoint the source of performance problems and get them resolved with providers.
Connect
◉ Internet traffic moves directly and securely from the user to the web and SaaS apps.
◉ Users can access frequently used internal apps without logging in to the VPN.
◉ SD-WAN “overlay” networks can seamlessly connect users, machines, and applications across clouds and data centers. An SD-WAN solution that is fully aware of SaaS applications can provide an optimal path to them by programming the network with the best path selection and adjusting it according to application and network telemetry.
Control
◉ Network administrators can enforce security and access policies consistently across remote locations.
◉ User identity and device health are verified before connecting to apps.
Converge
◉ Combining networking and security provides
observability across the environment, including the network, internet, and cloud. Administrators get actionable insights from every user and app over any network.
◉ Investigations and threat response are streamlined because of integrated security.
Use case 2: Secure edge
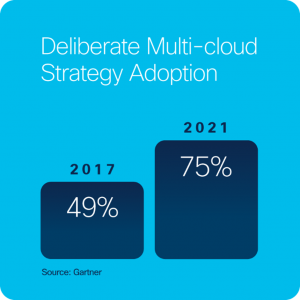
Multicloud environments, which use cloud services from more than one public cloud provider, are driving the need to secure the cloud and access edge.
Organizations adopt multicloud strategies in order to hit their business objectives and take advantage of cost savings and innovation while reducing risk. With distributed users needing to access applications in multiple clouds from anywhere, at any time, organizations must provide security closer to the user and edge to minimize network latency and stay agile.
Finding an optimal balance between protection and performance is challenging in cloud environments:
◉ Managing complexity: Multi-vendor cloud deployments bolted onto a traditional network architecture often lead to inconsistent performance and poor user experience.
◉ Resolving performance issues: Without visibility, it’s difficult to identify performance problems for end-users. Without insights, it’s difficult to know what action to take to solve them.
◉ Applying consistent security: Policies need to protect users, devices, and applications from the latest cyberattacks while being scalable for access from anywhere. Authentication needs to be seamless.
Again, SASE and SD-WAN solve these problems, safeguarding the network edge.
Connect
◉ Multicloud access is optimized for secure, consistent application performance.
◉ Cloud-delivered WAN architecture connects users to apps through a single fabric with zero-touch provisioning, intelligent path selection, and automated cloud connectivity.
Control
◉ Access to the internet is secure, fast, and reliable.
◉ Users access all applications through a zero-trust framework, whether they’re on-premises or in the cloud.
Converge
◉ Consumption is simplified and deployment is faster thanks to the integration of networking and security.
◉ Observability supplies actionable insights to resolve issues.
◉ A common cloud-delivered security policy is enforced consistently, everywhere.
Source: cisco.com