Tuesday, 2 April 2024
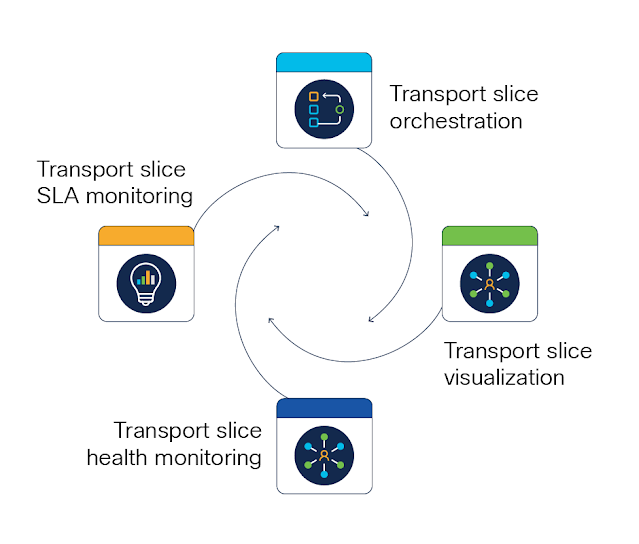
Pave the Way for New Revenue with Transport Slicing Automation and Assurance
Monday, 1 April 2024
Mastering CCNP Security 300-740 Exam: An In-Depth Look
In the ever-evolving field of network security, standing out as an IT professional requires not just skill, but validation of that skill. The CCNP Security 300-740 certification emerges as a beacon for those dedicated to mastering Cisco networks' security. This coveted credential is more than a certificate; it's a badge of honor that signifies your prowess in deploying and managing cutting-edge security measures in the cyber world.
Diving Deep into the CCNP Security 300-740 Exam
At the heart of the CCNP Security certification lies the 300-740 exam, a rigorous test that probes your knowledge across various pivotal security domains such as secure network access, content security, and navigating the complexities of cloud security. Crafted meticulously, the 300-740 SCAZT exam ensures that those who pass can shield network infrastructures against the threats of today and tomorrow.
300-740 SCAZT Exam Breakdown:
Duration: 90 minutes
Question Count: Between 55 to 65
Passing Score: Typically falls between 750 and 850 out of 1000
Format: A mix of multiple-choice and simulation-based questions
Validity: 3 years before renewal is required
CCNP Security Exam Preparation Pathways
Official Cisco Resources: Dive into the wealth of knowledge provided through Cisco's own training courses. These not only cover the theoretical aspects but also offer practical lab exercises.
Comprehensive Study Guides: Bolster your preparation with detailed study materials that go in-depth into each 300-740 exam topic.
Practice Makes Perfect: Regular practice exams are invaluable. They pinpoint areas needing improvement and familiarize you with the Cisco SCAZT exam's structure and pacing.
Community Engagement: Connect with peers through forums and study groups. Sharing insights and experiences can provide unique perspectives and study tips.
Best Tips to 300-740 Triumph
Know What's Expected: Thoroughly understanding the 300-740 SCAZT exam objectives can give you a clear roadmap of what to study.
Strategic Study Plan: Allocate your study time wisely, ensuring each topic gets the attention it deserves, with regular reviews.
Real-World Application: There's no substitute for hands-on experience. Create a lab environment to practice real-world security scenarios on Cisco networks.
Stay Informed: The cybersecurity landscape is dynamic. Keep abreast of the latest trends and technologies that could be included in the CCNP Security exam.
Career Advancement Post-Certification
Earning the CCNP Security 300-740 certification can significantly propel your career forward, marking you as a seasoned professional ready to tackle complex security challenges. Career doors that may open include roles as a Network Security Engineer, Security Analyst, Cybersecurity Specialist, or Network Administrator with a security focus.
Benefits of Being CCNP Security Certified:
Industry Credibility: CCNP Security certification is a gold standard in IT, highlighting your expertise in Cisco's security solutions.
Career Growth: It paves the way for advanced roles, showcasing your dedication to professional growth and security mastery.
Skill Enhancement: Preparing for the 300-740 SCAZT exam deepens your understanding of network security, from principles to best practices.
Salary Upside: Certified professionals often enjoy higher salaries and better job prospects.
Global Recognition: Cisco's certifications are acknowledged worldwide, opening international career opportunities.
Considering the Challenges:
Investment Required: Achieving certification comes with its costs, including exam fees and study materials.
Time Management: The extensive study required demands a significant time commitment.
Keeping Pace with Technology: As security technologies evolve, so must your knowledge, necessitating continuous learning.
Exam Rigor: The CCNP Security exam's challenging nature demands a solid grasp of complex concepts and hands-on experience.
Specialization: While highly valuable for those in network security, it might not offer the same benefits for individuals in non-Cisco environments or different IT areas.
Conclusion
The journey towards obtaining the CCNP Security 300-740 certification requires dedication, consistent studying, and practical application. It is a path that not only enhances your professional life but also distinguishes you as an expert in the vital field of network security. By embracing the challenge and making the most of the resources available, you can unlock a new realm of career opportunities and personal growth in the IT security domain.
Saturday, 30 March 2024
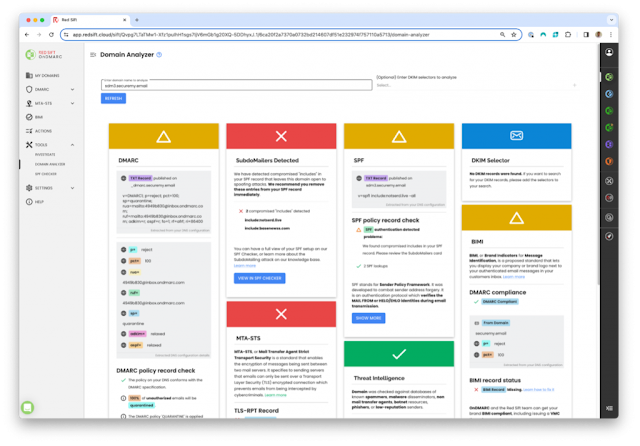
Hiding in Plain Sight: How Subdomain Attacks Use Your Email Authentication Against You
What’s happened?
What should I look out for?
Proactive steps to start today:
What else should I do?
Thursday, 28 March 2024
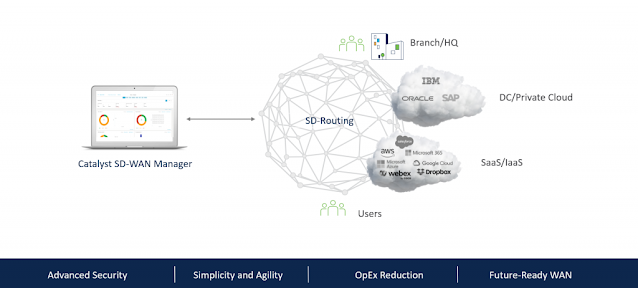
SD-Routing: Unlock Agility and Efficiency for the Secure WAN Edge
- Unify management: Manage device software upgrades, monitoring, and troubleshooting through the intuitive Catalyst SD-WAN Manager dashboard. This simplifies network operations and empowers you to manage both traditional routing and Catalyst SD-WAN environments.
- Tame legacy challenges: Simplify complex legacy operations with SD-Routing. Basic troubleshooting tools within the manager help you maintain and optimize performance. Continuous updates ensure your network stays ahead of the curve.
- Combat configuration drift: Manage and track changes with a unified platform. Use the manager to create configuration templates for standardized deployments and future SD-WAN migration.
Security
Cloud on-ramp for multicloud
Tuesday, 26 March 2024
GenAI will Transform B2B Interactions and Solutions in the Year Ahead with New Depth of Context and Control
Additional B2B considerations with GenAI
Moving fast towards contextual understanding and reasoning
Saturday, 23 March 2024
Increase Market Share Quickly with Cisco Specializations and GTM Tools
- Differentiate yourself from your competition by earning more Cisco Powered Services Specializations and pave your way to Gold-level advantages.
- Use your market development funds for business development, demand generation, funding headcount, and internal training.
- Leverage ready-made marketing kits and templates and get access to experts to help you grow your business.
- Earn greater pricing incentives and discounts that help you reach your revenue goals faster. Cisco continuously updates and adds marketing resources, so you can maximize your earning potential as your sales grow.
Growth drivers
Greater Together
Create marketplace differentiation with Cisco
- Proven blueprints: Validate your competency in areas including Power Hybrid Work, Secure the Enterprise, Transform Infrastructure, and Reimagine Applications.
- Quicker path to advancement: Meet specialization training requirements with up to 40 percent cost reductions. Role-share using CCIEs and CCNPs helps you meet Provider-level requirements faster.
- Showcase capabilities: Once you achieve these specializations, you gain access to industry-recognized logos and exclusive go-to-market resources to build successful solutions and services for Managed SD-WAN, Meraki, SASE, FSO, and many more.
- Sales acceleration: Expand your Cisco Powered Services portfolio and earn greater rewards within the Provider role, including exclusive upfront discounts and market development funds.