What customers are really asking is “Can I rely on the built-in security capabilities in Office 365 or do I still need to run a 3rd party email security solution such as a Secure Email Gateway?” And the answer — well that depends; every customer’s environment is different.
Do I have to go to the Cloud?
But first, let’s get the most common misconception out of the way. While it is more efficient to run your email security gateway in the cloud, close to your Office 365 tenancy, there is actually no technical reason why you can’t continue using your current on-premise email security appliances to also protect Office 365, during the migration and even afterwards. After all, it is just a matter of MX record addressing and routing, or in other words ensuring you have all the connections between your on-premise email security gateway which would be responsible for receiving all incoming email and Office 365 which would be hosting your users inboxes set correctly. Sure, this isn’t the most efficient method as you are tromboning or hair-pining traffic up and down and most organizations would only run in this mode for the time frame of the migration. If you already own the solution and have staff trained to support and manage it, it makes sense to see what value it adds to Office 365 first before you consider migrating to a cloud email platform, don’t change too much at the same time, let the Office 365 migration settle in first.
How to Answer the Question – For Your Environment
What a customer needs to do, whether its related to the Cisco Email Security solution or any other 3rd party solution, is to consider all the areas of Office 365 where these 3rd party solutions can supplement the base capabilities of Office 365. Don’t just ‘tick-box compare’ features. Look at all features and understand how they work. Can the Office 365 features do everything I need today and what I might need it to do tomorrow? Consider how you can address any gaps and what it means for your organization.
One example of how 3rd party email security gateways can add value to Office 365 is to consider spam quarantine management. In Office 365 there are essentially two ways that a user can get access to and manage quarantined email that have been classified as false positives. The most common method is via the Junk folder in their Outlook client, it can be difficult to search but generally works well. The second method is a web-based end-user quarantine system. Confusing, but the main issue is that there are very few categories of spam in Office 365. Either an email is categorized as spam or its not and this causes an issue on providing end-user spam management. There are very few controls about what end-users have access to and what they do not. Ideally, you’d likely rather not want your end-users making decisions around whether to release potentially malicious or inappropriate/pornographic content, you have to ensure you are providing a safe working environment for all employees.
Clearly security is the most important area of capability where we can supplement the core capabilities in Office 365. We have had many customers decide to just rely on Office 365 for email security only to come back several months later. What we have seen as a very common theme across these customers is that the first impact they see is at the help-desk which was not expected. The issue is that they have changed out one of the core security technologies that the organization had probably been using for years and become accustomed to, the spam detection engine. Most of the leading email security providers do a pretty good job today, I couldn’t tell you the last time I had a spam message in my inbox. Suddenly the new spam detection engine is letting through some spam, users can’t remember what to do with spam, so they call the help-desk, all at once! Then after that initial rush, end-users start to notice some email possibly missing and now the help-desk are doing (learning in a hurry) message tracking looking for false positives.
A perfect example of a misstep many organizations make by doing a ‘tick-box’ comparison is that a feature like a spam detection engine can have significantly different capabilities depending on the vendor. Cisco Email Security has been innovating our email security solution for over 20 years. Our world class threat intelligence is supplied by the largest non-government threat research organization in the world, Talos.
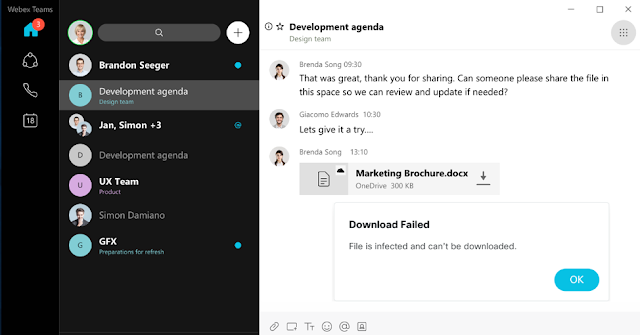
There are many other areas in email security to consider; known malware recognition, unknown or suspect attachment handling, embedded URL handling, support for external threat intelligence and active content disarm and reconstruction. All these functions make meaningful differences in keeping the bad stuff out and your inboxes safe.
Also consider how easy your system is to manage. What reports have you come to rely on in your old systems, what are your managers expecting to see? Have you tested Office 365 to see what it’s like to do message tracking? Have you created email policies?
How confident are you in the capability of the policy engine? Are you even confident that you can recreate all your current email policy in Office 365? What policies will you need in the future? In our experience, in addition to reporting, this is the other area often not tested extensively enough in initial evaluations. With the growing amount of regulatory compliance regulations, having an advanced policy engine with plenty of policy conditions and actions coupled with significant flexibility is more likely to support your efforts. While the Cisco policy engine currently has 24 conditions and 26 actions within its content filtering policy engine, it’s what those options are that make the difference. For example, full control over adding/editing header information and the ability to reroute email based on policy are a couple of options that we see organizations using for a variety of business enablement projects. Our customers are getting real business value out of their email security solution, and the options themselves; another example of how dangerous it is to box tick!
Suggested Decision Process
So now that we have some understanding of what we should be looking at, what’s the best way to go about this analysis? Below are a series of steps to consider to help you make an informed decision:
1. Your current email policy: This is a great opportunity to assess all the policies and settings that you are relying on now. Are they all needed going forward? What have you seen or tested for yourself that is supported by Microsoft?
2. Email security capabilities: How these technologies work on your email flow is what is important. There are many ways of validating this by either running different solutions in a monitoring only mode or Bcc’ing/copying email to the solution under test for analysis and then deletion. Is Office 365 by itself blocking everything you need? If it is missing some email, is that critical for your organisation? What sort of impact could result in certain types of email getting through to end-users? (Missed spam, malicious attachments, inappropriate content, malicious URL’s, advanced phishing attacks etc?).
3. Advancing Phishing detection: Phishing has been a scourge for years because it is constantly evolving. The latest iteration, BEC or Business Email Compromise, has financially impacted many organisations large and small all around the world. BEC is difficult to detect, includes no attachments or embedded URL’s and is sent in low numbers and in a very targeted way. Has your company had issues? Do you know someone who has? What could the impact be for you? Does your current solution have any specialist support for BEC? Have you measured how much that is catching and are you sure that Office 365 would be able to detect and block these even using the advanced phishing capabilities in Microsoft’s ATP optional add-on? This in particular is a great area to potentially leverage a specialist solution such as Cisco’s Advanced Phishing Protection module which can work in any email environment.
4. Management: How easy is the solution to use? Can you track a message all the way through the scanning process? Can the search engine easily find and release quarantined email? Are you using end-user spam management now? Do you want to continue to use it? Will the capability offered in Office 365 meet your HR driven employee policies and requirements?
5. Reporting: Do you have any automatic scheduled reports being sent within your organization; perhaps to senior management? Can these be replicated within just Office 365? What reporting, or compliance auditing requirements can you see being required in the short term? Are these reports supported?
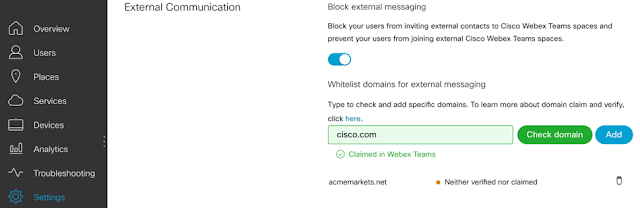
6. External Domain Protection: Becoming a more common inclusion for corporate messaging teams, organizations are using DMARC and related standards to monitor which organizations are sending email using your domain. Is your brand being negatively affected by being used in phishing attacks? While Office 365 does not offer any capability here, this is another area that can be addressed or supplemented using standalone products or solutions such as Cisco Domain Protection.
Licensing & Recommendations
For the majority of our customers, the ideal combination is Office 365 E3 with Cisco Cloud Email Security. This combination includes all the core Office 365 products supplemented with an enterprise class email security solution. The ATP features for Safe Links and Safe Attachments are easily met and exceeded in Cisco’s Cloud Email Security, this is the combination that Cisco itself runs.
Moving up to the E5 licensing tier is a difficult decision, you need to look at all the inclusions you get, which are substantial and determine what value your organisation would get out of these. From an email security & management viewpoint everything is pretty much covered with the combination recommended above except for the advanced email archiving capability if you need that over the basic option in E3.
There are also of course all the collaboration/telephony services which Cisco has great solutions for as well!
Options for Proving the Value
So how can you prove the decision you are making is the right one, or at least if you have already deployed Office 365 by itself, test to see how it is performing from a security viewpoint at least?
Cisco has an analysis tool called “Threat Analyzer for Office 365” and it works by accessing a selection on your user’s inboxes (you define which ones) via the Microsoft Graph API built into Office 365. Threat Analyzer scans these inboxes using the same email security engines that we have in our commercial offerings, looking for any email that we would have detected as Spam, Gray-mail, Malicious Email (with attachment or embedded URL) or inappropriate spam. Threat Analyzer does not do anything to this email or the inbox, it just records what the Cisco email security engines would have detected and then produces a report showing these results. From this report you can get an idea of the extra value you would get from running Cisco email security together with Office 365. However, it needs to be remembered that not all the security engines can be used (Connection filtering for example) with a configuration such as this, so your final experience would be even better than the report would suggest.
There are also other options, the recommended option would be to have Cisco email security running in front of Office 365 so it is the internet facing email server for your email domains, this way 100% of the Cisco security capability can be brought to bear. You can test this by using the default policy which would detect/block & quarantine within Cisco email security, or you simply tag email for it to be then processed by Office 365 and see the combined results. We have also seen other organizations creating a BCC rule within Office 365 to copy all email that is to be delivered to end-users also copied to Cisco email security to see what would have been blocked as well, although this also limits the security engines that can be used as it is also not internet facing, the same limitation that Threat Analyzer for Office 365 has.