At last year’s Partner Summit, Cisco Channel Chief Oliver Tuszik talked about how partners can “own their edge” to uniquely differentiate themselves and help them perform today while transforming for the future. You may also recall his hilarious comparison to a monkey. Although he and the monkey share 99% of the same DNA, the 1% makes them very different beings. That 1% difference in a business context is a competitive advantage that leads to greater partner margin, revenue, and material business outcomes for customers. It is why differentiation is a big focus for Cisco and our partners.
When we talk about differentiation within the Strategic Partner Organization, we’re referring to how we work with our global partners to create a unique competitive advantage that showcases our joint capabilities for customers. How do we do this? We use a combination of co-developing technology, integrating platforms with APIs, creating new go-to-market initiatives, and building new solutions and joint architectures that open up new buying center budgets within customers. This differentiation is the secret sauce that gives Cisco and our partners the competitive edge to deliver business outcomes.Differentiation at Work
Here are a few real-world examples of how Cisco and some of our global strategic partners are driving differentiated business outcomes:
NTT
NTT Ltd. provides customers with outcome-based solutions powered by investments and strategic collaboration with Cisco. Our partnership centers around the joint development of consumption and adoption models for software (and services) that delivers on the promise of client-centric, data-driven, managed services. Seamless access to accurate and actionable data is the key differentiator for NTT Ltd., which is integrating more than 160 APIs and telemetry from Cisco platforms, products and programs into their service layer and managed center portal. API integration and telemetry allow customers to realize the full value of software licenses, easily track ROI and build new opportunities for innovation and growth, while ensuring a delightful, data-driven customer experience.
SAP
Through Cisco’s AppDynamics Business IQ for SAP, customers can visualize their SAP application performance and measure how that performance impacts their business health. The solution, which also monitors non-SAP business processes, uses machine learning algorithms to flag operation bottlenecks and provide root cause analysis so customers can remediate the issue. Read our SAP Partner Executive Robert Madl’s August blog “Monitoring SAP Business Processes with Cisco AppDynamics” for more details.
Schneider Electric Industries
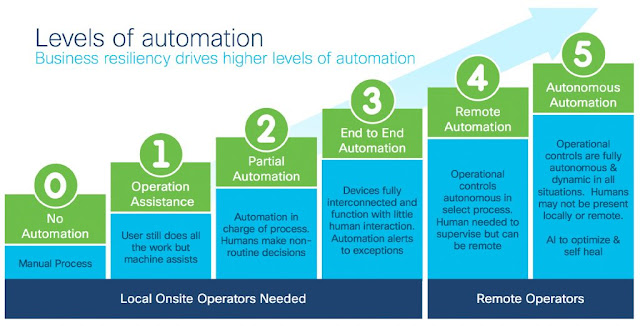
Industry 4.0 is enabling digital transformation and delivering business outcomes such as increased agility and productivity gains while reducing operating costs for customers in manufacturing and industrial plants. Cisco and Schneider Electric Industries are committed to take advantage of this market with our joint differentiated solution architecture EcoStruxureTM. Our latest offer, SecureConnect EcoStruxure, leverages Schneider’s market leading IIoT applications integrated with Cisco’s industrial networking, edge intelligence and end-to-end security solutions. It was recently deployed by a large global mining company, which used asset optimization and asset tracking. Additional industry use cases include predictive maintenance and remote monitoring.
Deloitte
Another example of partner differentiation is the collaboration between Cisco and Deloitte. We team together to leverage Deloitte’s cyber strategy and transformation experience with Cisco’s industry leading security portfolio of products. Combining our joint strengths, we helped a large healthcare provider bridge security capability gaps, identify and align on key security priorities, and achieve security objectives through a Security Enterprise Agreement (EA) Value Assessment. The Assessment is designed to provide an objective third-party evaluation of EA value over the agreement’s term, providing customers with data to develop an actionable strategy to realize the highest value of a Cisco Security EA.
NetApp
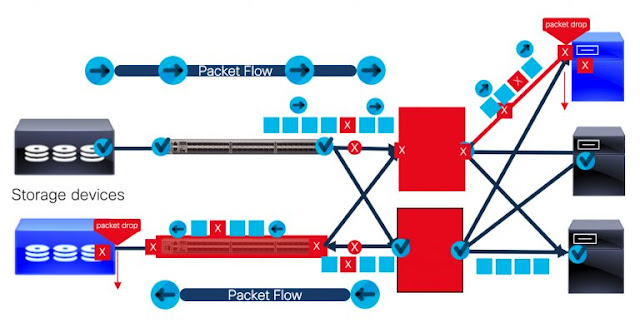
Our customers live in a hybrid cloud world. They seek consistent and reliable ways to manage their data—whether in the data center, at the network edge or in the public cloud. You’re likely aware that Cisco and NetApp’s converged infrastructure platform FlexPod has supported mission critical applications for over a decade. But did you know that FlexPod offers an elegant solution for modern, hybrid cloud environments? FlexPod leverages NetApp’s Data Fabric, a part of their ONTAP storage operating system, to accelerate digital transformation by simplifying and integrating data management across cloud and on-premise environments.