As many organizations are looking at wireless refreshes that include both expansion and upgrades to Wi-Fi 6, those with small, medium or branch locations have some cool (and very useful) new options to consider and should seriously rethink the deployment model.
Historically, small, medium and branch wireless deployments have been an operational challenge for many organizations. Some of those challenges include:
◉ Solution cost including procurement, deployment, and maintenance,
◉ Management complexity
◉ Lack of visibility into the user experience
◉ Limited feature sets, including security limitations, that force a compromise on features in smaller sites to uphold cost effectiveness
◉ Approaching smaller sites as home Wi-Fi setups for lack of better solutions
I wanted to emphasize that size does not matter, meaning that the deployments representing smaller locations can easily represent significant cash flow where user experience is key. I have personally struggled in the past with the need to purchase multiple wireless controllers for sites with 10 to 20 access points.
Today, things are looking a little different for smaller enterprise grade deployments. Cisco’s latest enhancements of the Cisco Embedded Wireless Controller (EWC) licensing model means its easy and cost effective to deploy these smaller networks without the need for a physical or even a cloud-based controller. Some might say it’s a game changer, and for those with small to medium wireless deployments up to 100 access points, it really is.
It is important to note that 100 access points is a large site. In my opinion, most deployments will consist of a handful of access points but it’s good to know the EWC can scale up to 100 APs if needed. Add in Cisco’s recent announcement that AireOS is going into sunset mode and you can see why EWC is a much-needed solution to support smaller sites. It also provides an exit strategy for some of the smaller site controllers like the 2504.
Full featured wireless controller integrated into the AP
As stated earlier, I think it is time to reinvent how we think and deploy these smaller wireless networks. With EWC we have the full enterprise features and management capabilities of a standalone (HA capable) controller(s), integrated into the Cisco Catalyst 9100 series access points. Previous embedded solutions were somewhat cumbersome to use and suffered feature parities, I know this because I’ve used them. With the latest EWC capabilities, Cisco really scored a home run thats worthy of taking a closer look at.
The EWC leverages the same IOS-XE software that runs on the Cisco Catalyst 9800 wireless controllers, so what you get is essentially controller without the appliance or licenses. And beyond supporting Catalyst APs, the EWC also supports many of Cisco’s existing AC Wave 2 access points including the 18xx, 28xx, 38xx, 48xx. While these Aironet APs can be part of the EWC network serving clients, they cannot function as the EWC controllers, that privilege is reserved for the Catalyst 91oo series access points.
With the EWC you can move to the new 9800 platform and still make use of your older access points.
Getting started
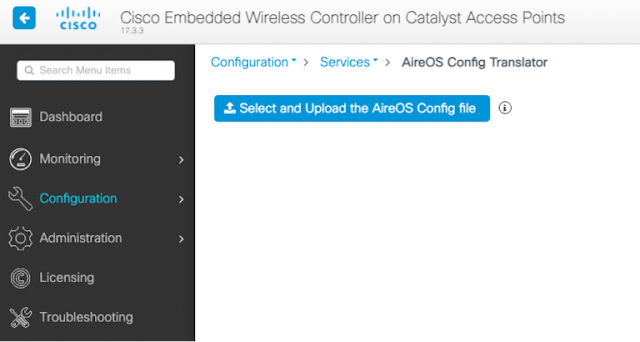
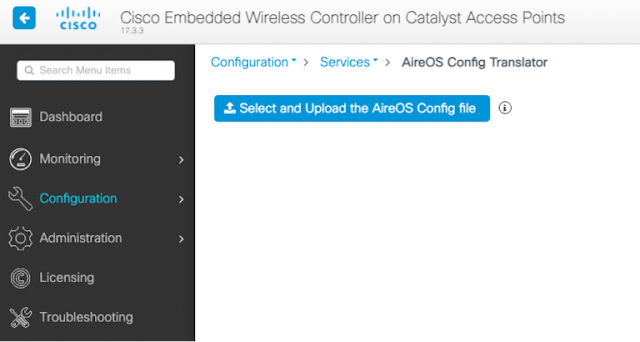
I find it’s best to start by adding two Catalyst 9100 EWC access points to your network as an HA controller pair. This gives you the flexibility to upgrade the rest of the access points as needed, on your timeline and budget. Making the migration process even easier, the EWC GUI has a configuration conversion utility that allows you to take your AireOS configuration and migrate it to the new Catalyst 9800 wireless controller platform configuration; it’s a quick process that saves a ton of time and effort. What makes this solution especially cool is that the EWC access points can be used as both a controller and to service clients, without any noticeable lag or experience issues.
Requirements and settings
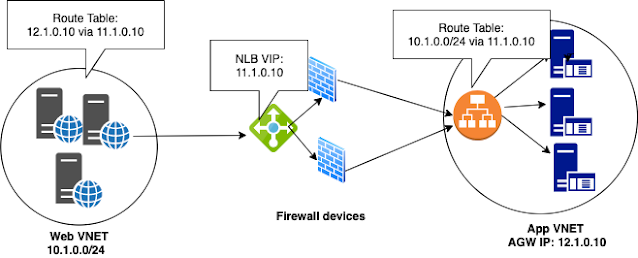
The EWC deployment resembles FlexConnect local switching mode, meaning the controller is only the control plane and all data originates from the wireless access points onto the network. You can change the access point mode to a trunk interface if you use AAA override or utilize multiple VLANS.
While you can run the EWC network with a single access point, if you installed at least two Catalyst EWC access points, they auto enable High Availability mode and if the wireless network can continue to operate and be fully managed if one of the EWC access points becomes unavailable.
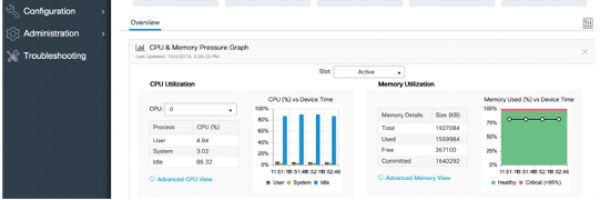
Now given the EWC is running the Cisco Catalyst 9800 software you have full access to all the enterprise features you would expect. This includes DNA Center for monitoring, Assurance, AI/ML and management, DNA Spaces for location services and engagement. For sites with higher security requirements, Cisco Umbrella is also available. Please note, these capabilities do not come standard with the EWC and require additional licensing, and in the case of DNA Center, a physical appliance.
What else is exciting, is that with the purchase of DNA licensing, you can turn on the multi-site management feature. This means that you can have multiple sites each with at least one EWC access point and manage them as a single network across all sites. This allows for some level of wireless service survivability if one of the sites loses connectivity to the WAN but still has Internet access. Multisite capabilities can also create a uniform user experience across all sites.

What comes standard the EWC is a host of tools that make setting up and maintaining your small but critical wireless network easy and cost-effective while providing Cisco enterprise-class features, security, and reliability.
Source: cisco.com