Embarking on the journey to earn a Cisco certification, especially one as pivotal as the 300-420 ENSLD, is a significant undertaking. The Designing Cisco Enterprise Networks exam is renowned for its comprehensive scope and the depth of knowledge it demands from candidates. Many aspiring network professionals approach this challenge with enthusiasm, only to find their meticulously crafted study plans falter, leaving them frustrated and often unsuccessful. But what exactly causes these setbacks, and more importantly, how can you ensure your preparation for the Cisco 300-420 ENSLD exam leads to a triumphant pass?
This long-form article is your definitive guide to understanding the common pitfalls in 300-420 ENSLD study plans and, crucially, how to build a robust, effective, and resilient strategy that will set you apart. We'll delve into the nuances of the exam, dissect the reasons for widespread failure, and provide a practical, step-by-step framework to engineer your success. By the time you finish reading, you'll have a clear roadmap to navigate the complexities of the Cisco 300-420 ENSLD exam topics and emerge with the confidence to ace it.
Understanding the 300-420 ENSLD Exam: Designing Cisco Enterprise Networks
The 300-420 ENSLD exam, officially known as Designing Cisco Enterprise Networks, is a specialist exam for the prestigious Cisco CCNP Enterprise certification. It validates a candidate's knowledge of enterprise design, including advanced addressing and routing solutions, advanced enterprise campus networks, WAN for enterprise networks, network services, and automation. This certification is a testament to your ability to design robust, scalable, and secure enterprise network architectures.
Exam Details at a Glance
- Exam Name: Designing Cisco Enterprise Networks
- Exam Code: 300-420 ENSLD
- Exam Price: $300 USD
- Duration: 90 minutes
- Number of Questions: 55-65
- Passing Score: Variable (approximately 750-850 out of 1000)
Successfully passing the 300-420 ENSLD demonstrates not just theoretical understanding but also practical design considerations crucial for modern enterprise environments. It's a stepping stone to advanced roles in network architecture and engineering.
The Cisco ENSLD Certification Syllabus: A Closer Look
To truly conquer the 300-420 ENSLD exam, you must have an intimate understanding of its syllabus. Cisco clearly outlines the percentage weighting for each domain, providing valuable insight into where you should focus your efforts. These percentages reflect the relative importance and prevalence of each topic on the exam:
- Advanced Addressing and Routing Solutions - 25%: This section covers complex IP addressing schemes, advanced routing protocols (OSPF, EIGRP, BGP), route redistribution, and route manipulation techniques vital for large-scale enterprise networks.
- Advanced Enterprise Campus Networks - 25%: Focuses on campus design principles, including Layer 2 and Layer 3 design, high availability mechanisms (FHRP), wireless design considerations, and network virtualization techniques like VRFs.
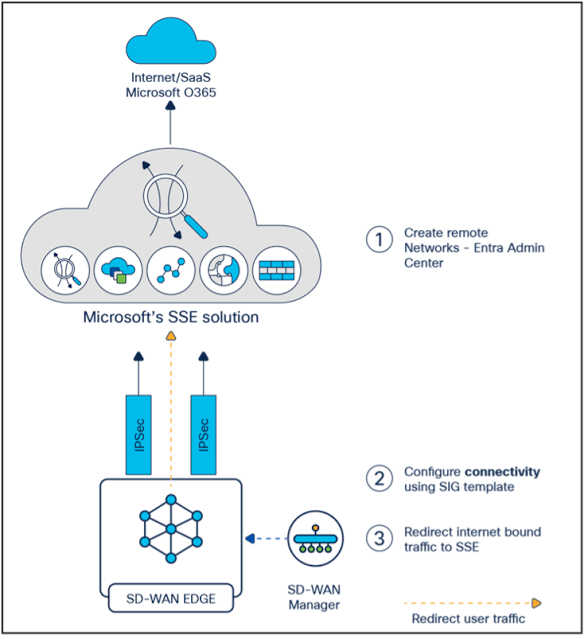
- WAN for Enterprise Networks - 20%: Explores various WAN technologies and design options, such as SD-WAN, DMVPN, MPLS, and Internet VPNs, along with their respective design implications for performance, security, and reliability.
- Network Services - 20%: Covers critical network services like QoS, network security design (firewalls, IPS/IDS integration), network programmability features, and overlay technologies.
- Automation and Artificial Intelligence - 10%: While a smaller percentage, this section is increasingly important, covering concepts like SDN, APIs, configuration management tools (Ansible, Puppet, Chef), and the role of AI in network operations and design.
Each of these domains requires a deep dive, not just into configuration, but into the *design principles* that dictate their implementation within an enterprise context.
Common Reasons 300-420 ENSLD Study Plans Fail
Despite the best intentions, many candidates find their 300-420 ENSLD study plans crumbling under the pressure. Recognizing these common pitfalls is the first step toward crafting a resilient plan that avoids them.
1. Lack of a Clear Understanding of Exam Objectives
One of the most frequent reasons for failure is not truly understanding what the exam expects. Candidates might study broad networking topics, but without aligning their efforts precisely with the official 300-420 ENSLD exam topics, they risk wasting time on irrelevant material or, worse, overlooking critical areas. The exam isn't just about knowing protocols; it's about designing solutions.
2. Inadequate Time Management and Unrealistic Schedules
The 300-420 ENSLD is a challenging exam. Many candidates underestimate the time required for comprehensive preparation. They create schedules that are either too aggressive, leading to burnout, or too lax, resulting in insufficient coverage of the syllabus. Life commitments often interfere, and a rigid, unforgiving schedule quickly becomes unsustainable.
3. Over-reliance on Brain Dumps or Poor-Quality Materials
The temptation to use brain dumps for quick answers is strong but ultimately self-defeating. While they might provide some answers, they fail to build the foundational understanding and critical thinking skills necessary for actual network design and for passing a challenging exam like the 300-420 ENSLD. Poor-quality study materials, whether outdated or inaccurate, also lead to confusion and incorrect learning.
4. Neglecting Practical Experience and Hands-on Labs
Network design isn't purely theoretical. Many candidates make the mistake of focusing solely on reading and memorization, skipping the essential hands-on practice. Without lab experience, the theoretical knowledge remains abstract, making it difficult to understand real-world design implications, troubleshoot scenarios, or apply concepts effectively, which are crucial for the Designing Cisco Enterprise Networks exam.
5. Ignoring Self-Assessment and Mock Exams
Failing to regularly assess progress is a critical error. Candidates often delay taking practice tests until the very end, missing valuable opportunities to identify weak areas early on. Mock exams, like those found with Cisco 300-420 ENSLD exam questions, are not just for checking knowledge; they are vital for time management practice, understanding question formats, and building exam-day stamina.
6. Poor Grasp of Foundational Concepts
The 300-420 ENSLD builds upon core networking principles. If a candidate has gaps in their foundational knowledge (e.g., subnetting, basic routing, switching), they will struggle immensely with the advanced design topics. Attempting to build a complex structure on a weak foundation is a recipe for disaster.
7. Not Adapting the Study Plan
A study plan should be a living document, not a static one. Many candidates stick rigidly to their initial plan, even when it's clearly not working or when their progress reveals unexpected strengths or weaknesses. The inability to adapt and refine the plan based on ongoing assessment can severely hinder progress.
8. Lack of Motivation or Burnout
The sheer volume of information and the complexity of the topics can be daunting. Without sustained motivation, regular breaks, and a healthy balance, burnout is a real risk. This often leads to procrastination, reduced study quality, and eventually, abandoning the study plan altogether.
Crafting Your Winning 300-420 ENSLD Study Plan
Now that we've identified the common pitfalls, let's construct a study plan designed for success. Your journey to passing the 300-420 ENSLD will be systematic, practical, and adaptable.
Step 1: Deep Dive into the Official Blueprint and Exam Objectives
This is your non-negotiable starting point. Go to the official Cisco Learning Network page for the 300-420 ENSLD exam. Download and thoroughly review the exam topics. Don't just skim them; break down each objective. Ask yourself:
- What specific technologies are mentioned?
- What are the verbs used (e.g., "describe," "implement," "design," "troubleshoot")? This indicates the expected level of understanding.
- How does each objective relate to real-world enterprise network design scenarios?
Map these objectives against your current knowledge. Highlight areas where you feel confident and, more importantly, areas where you have gaps. This initial assessment will form the backbone of your personalized 300-420 ENSLD study guide.
Step 2: Create a Realistic and Flexible Study Schedule
Based on your assessment from Step 1 and your personal commitments, develop a study schedule. Be honest about how much time you can realistically dedicate each day or week. Factor in:
- Duration: How many weeks or months will you need? For a 300-420 ENSLD, a 3-6 month timeline is often realistic for those balancing work and study.
- Daily/Weekly Blocks: Allocate specific time slots for study. Consistency is more important than intensity. Even 1-2 hours daily can be highly effective.
- Topic Allocation: Distribute the syllabus topics according to their weighting and your current knowledge gaps. For instance, dedicate more time to the 25% sections on Advanced Addressing and Routing or Advanced Enterprise Campus Networks.
- Buffer Time: Always build in buffer days or weeks for unexpected delays, deeper dives into complex topics, or simply to catch up.
- Review Sessions: Schedule regular review periods (e.g., end of week) to reinforce what you've learned.
Remember, flexibility is key. If a topic takes longer than expected, adjust subsequent timings. Don't be afraid to revisit and refine your schedule as you progress.
Step 3: Curate High-Quality Study Materials
Your choice of resources can make or break your study plan. Prioritize official and reputable sources:
- Official Cisco Press Books: These are often the most comprehensive and aligned with exam objectives. Look for specific 300-420 ENSLD study material.
- Cisco Learning Network: This is an invaluable resource for exam topics, study groups, and official documentation.
- Cisco Training Courses: Consider official Cisco training courses or reputable third-party providers that offer structured learning for the Designing Cisco Enterprise Networks exam prep.
- Online Documentation: Cisco's documentation (white papers, design guides, configuration guides) is essential for in-depth understanding.
- Practice Questions and Labs: Seek out high-quality practice questions, like those available through NWExam's Cisco 300-420 ENSLD sample questions, and lab exercises that simulate real-world design challenges.
For additional resources and insights, make sure to check out our broader collection of networking tips and guides on CiscoCentral Blog, your go-to hub for all things Cisco.
Step 4: Master Each Syllabus Topic Systematically
Approach each section of the 300-420 ENSLD syllabus methodically. Don't jump around. For each topic:
- Conceptual Understanding: Start with the foundational concepts. Understand the "why" before the "how."
- Design Principles: Focus heavily on the design considerations. Why would you choose one solution over another? What are the trade-offs? This is crucial for the ENSLD exam.
- Implementation Details: While this is a design exam, having a solid grasp of how technologies are implemented helps you understand their design implications.
- Hands-on Application: Immediately move to labs to solidify your understanding.
Let's briefly outline how to approach each major topic area:
Advanced Addressing and Routing Solutions (25%)
Mastering this segment means going beyond basic routing. Dive deep into BGP path attributes, OSPF area types, EIGRP variance, route summarization, and redistribution design. Understand how these elements impact network scalability, performance, and stability in large enterprises. Practice manipulating routing updates and designing redundant routing paths.
Advanced Enterprise Campus Networks (25%)
This section is about designing high-performance, resilient campus environments. Study multi-layer campus design, including access, distribution, and core layers. Focus on topics like VSS, StackWise, HSRP/VRRP/GLBP, and advanced spanning-tree configurations. Understand wireless design principles, QoS implementation in the campus, and network segmentation using VLANs and VRFs.
WAN for Enterprise Networks (20%)
Given the rise of hybrid workforces and cloud services, WAN design is more critical than ever. Explore SD-WAN architectures, different DMVPN phases, MPLS VPN options, and secure Internet connectivity using VPNs. Understand the design implications of each technology in terms of cost, performance, security, and management. Design solutions for branch connectivity and remote access.
Network Services (20%)
This domain involves integrating essential services into the network design. Deep dive into QoS mechanisms (classification, marking, queuing, shaping, policing) and their placement. Understand security design principles, including firewall placement, IPS/IDS integration, and secure access solutions. Explore network virtualization techniques and how they enhance service delivery and security.
Automation and Artificial Intelligence (10%)
Though the smallest percentage, this is a growing area. Understand the basics of network programmability, APIs, and configuration management tools (Ansible, Puppet, Chef, Python scripting). Focus on how these tools can automate design deployment, verification, and operations. Grasp the concepts of SDN (Software-Defined Networking) and the potential of AI/ML in network design and troubleshooting.
Step 5: Integrate Hands-on Practice Extensively
Theory without practice is insufficient for the 300-420 ENSLD. You need to build, break, and fix networks to truly internalize design concepts. Invest time in hands-on labs using:
- Cisco Modeling Labs (CML): Cisco's official network simulation platform.
- EVE-NG or GNS3: Powerful emulation platforms that allow you to build complex multi-vendor topologies.
- Physical Hardware: If accessible, working with real Cisco routers and switches provides invaluable experience.
Focus on lab scenarios that challenge your design knowledge. Don't just follow instructions; try to design a solution from scratch based on a given set of requirements. Practice verifying your designs and troubleshooting common issues. This practical application solidifies your understanding of the Cisco 300-420 ENSLD exam topics.
Step 6: Regular Self-Assessment and Mock Exams
This step is crucial for identifying weaknesses and building confidence. Implement a regular cycle of study, practice, and assessment:
- Quizzes: After covering a sub-topic, take short quizzes to test your immediate recall.
- Chapter Reviews: At the end of each major syllabus section, conduct a thorough review and take a comprehensive quiz.
- Full-Length Mock Exams: As you get closer to your exam date, take several full-length 300-420 ENSLD practice tests under timed conditions. This simulates the actual exam environment and helps you manage your time effectively.
Analyze your results meticulously. Don't just look at the score; review every incorrect answer. Understand *why* you got it wrong. Was it a knowledge gap, a misinterpretation of the question, or a time management issue? This feedback loop is essential for refining your 300-420 ENSLD study guide and focusing on weaker areas.
Step 7: Join a Study Community
You don't have to go it alone. Engaging with a study community offers numerous benefits:
- Peer Support: Connect with others also preparing for the Designing Cisco Enterprise Networks exam. Share challenges, insights, and motivation.
- Clarification: If you're stuck on a concept, a community forum (like the Cisco Learning Network) can provide quick answers and alternative explanations.
- Diverse Perspectives: Hearing how others approach design problems can broaden your understanding.
- Accountability: Being part of a group can help you stay on track with your study goals.
Look for online forums, Discord servers, or local study groups dedicated to Cisco certifications.
Step 8: Review, Refine, and Stay Flexible
Your study plan is dynamic. As you learn and grow, your plan should evolve. Periodically:
- Review Your Progress: Are you hitting your milestones? Are certain topics taking longer than expected?
- Adjust Your Schedule: Don't be afraid to add more time to difficult sections or redistribute time if you've mastered something quickly.
- Revisit Weak Areas: Use your assessment results to direct your focus. It's better to spend extra time shoring up weaknesses than to passively review strengths.
- Stay Hydrated, Rested, and Mindful: Burnout is real. Take regular breaks, ensure you get enough sleep, and maintain a healthy lifestyle. A fresh mind absorbs information better.
Key Strategies for Success on the 300-420 ENSLD Exam
Beyond the structural elements of your study plan, adopting certain learning strategies can significantly boost your chances of success.
- Active Learning: Don't just passively read. Take notes, summarize concepts in your own words, create flashcards, and try to teach the material to someone else (even if it's just your rubber duck!).
- Spaced Repetition: Review previously learned material at increasing intervals. This helps move information from short-term to long-term memory.
- Prioritize Weak Areas: It's tempting to study what you already know well. Resist this urge. Dedicate extra time and effort to topics you struggle with.
- Maintain Well-being: Adequate sleep, regular exercise, and a balanced diet are crucial for cognitive function and sustained focus.
- Positive Mindset: The 300-420 ENSLD is difficult, but it's achievable. Believe in your abilities, stay persistent, and visualize success.
Benefits of Achieving Cisco ENSLD Certification
Passing the 300-420 ENSLD exam is more than just earning a certificate; it's an investment in your career. The benefits are substantial:
- CCNP Enterprise Certification: The ENSLD is a core component of the CCNP Enterprise certification, elevating your professional standing.
- Career Advancement: This certification validates your expertise in enterprise network design, opening doors to advanced roles such as Network Architect, Senior Network Engineer, and Solutions Designer.
- Deepened Design Skills: You'll gain a comprehensive understanding of complex design principles, enabling you to create scalable, resilient, and high-performing networks.
- Increased Earning Potential: Certified professionals often command higher salaries due to their specialized knowledge and validated skills.
- Industry Recognition: Cisco certifications are globally recognized and respected, signaling your competence to employers worldwide.
The 300-420 ENSLD prerequisites involve a strong foundation in networking, often equivalent to a CCNA, but the exam itself pushes your design capabilities to the next level.
Conclusion
The 300-420 ENSLD, Designing Cisco Enterprise Networks exam, is a formidable challenge, but it is far from insurmountable. Most study plans fail not because the candidates lack intelligence or dedication, but because their approach is flawed. By understanding the common pitfalls and consciously building a study plan that addresses them head-on, you can dramatically increase your chances of success.
Remember to meticulously dissect the exam topics, create a realistic and flexible schedule, prioritize high-quality study materials, and commit to extensive hands-on practice. Regular self-assessment, engagement with a study community, and continuous refinement of your plan are not optional; they are essential for mastering the Cisco ENSLD certification syllabus. With persistence, a smart strategy, and the right resources, your 300-420 ENSLD study plan won't just avoid failure – it will lead you straight to success. Start designing your future today.
Frequently Asked Questions (FAQs)
1. Is Cisco 300-420 ENSLD difficult?
Yes, the 300-420 ENSLD is considered a challenging professional-level exam. It requires a deep understanding of enterprise network design principles, not just configuration, and covers a broad range of advanced topics.
2. What is the 300-420 ENSLD pass score?
The passing score for the 300-420 ENSLD exam is variable but typically falls between 750-850 out of 1000. Cisco uses a statistical analysis to determine the cut score, which can fluctuate slightly.
3. Where can I find the best study material for Cisco 300-420 ENSLD?
The best study materials include official Cisco Press books, the Cisco Learning Network, official Cisco training courses, and reputable third-party video courses. Supplement these with extensive lab practice using CML or EVE-NG.
4. What are the Cisco 300-420 ENSLD prerequisites?
While Cisco doesn't enforce strict prerequisites, a strong understanding of networking fundamentals, typically equivalent to a CCNA certification, is highly recommended. Experience with enterprise-level routing and switching is also beneficial.
5. How important is hands-on practice for the 300-420 ENSLD exam?
Hands-on practice is critically important. The ENSLD exam focuses on design, and practical experience with implementing and troubleshooting network components helps solidify your understanding of design implications and best practices. Lab work is essential for success.