For those of us in security operations, it could be easy to feel discouraged. After all, it’s an unfair fight. The bad actors seem to have unlimited time and budget. And we certainly don’t!
But here’s some good news: one of the most valuable tools available in threat hunting is free. Just like the golden oldie tune (or the Janet/Luther pop classic) says, the best things in life don’t always cost money. For customers with Cisco Next-Generation Firewalls, Intrusion Prevention (IPS), AMP for Endpoints, Cisco Umbrella, Email Security, and/or Threat Grid, Cisco Threat Response helps detect, investigate, and take corrective action against cyber threats—at no additional cost.
We work with security professionals in organizations of all types and sizes. No matter their differences, they all say they’re bombarded. They wish they could “hit pause” on the flood of security events to allow for the time-consuming manual work they have to do after an attack. Not only that, they’re often in the difficult position of having to make decisions with inadequate information. They’re concerned about blocking too much and compromising productivity. Or not blocking enough to protect the business.
Cisco Threat Response provides an automated process to help. It’s a key pillar of Cisco’s integrated security architecture and designed to give you the contextual awareness you need so you can see, investigate, and act on threats fast. If you’ve invested in Cisco security products that support it, Threat Response is on your side to make the fight against cyberattacks a little fairer.
But here’s some good news: one of the most valuable tools available in threat hunting is free. Just like the golden oldie tune (or the Janet/Luther pop classic) says, the best things in life don’t always cost money. For customers with Cisco Next-Generation Firewalls, Intrusion Prevention (IPS), AMP for Endpoints, Cisco Umbrella, Email Security, and/or Threat Grid, Cisco Threat Response helps detect, investigate, and take corrective action against cyber threats—at no additional cost.
Making the Fight More Fair
We work with security professionals in organizations of all types and sizes. No matter their differences, they all say they’re bombarded. They wish they could “hit pause” on the flood of security events to allow for the time-consuming manual work they have to do after an attack. Not only that, they’re often in the difficult position of having to make decisions with inadequate information. They’re concerned about blocking too much and compromising productivity. Or not blocking enough to protect the business.
Cisco Threat Response provides an automated process to help. It’s a key pillar of Cisco’s integrated security architecture and designed to give you the contextual awareness you need so you can see, investigate, and act on threats fast. If you’ve invested in Cisco security products that support it, Threat Response is on your side to make the fight against cyberattacks a little fairer.
Getting started with Cisco Threat Response is easy.
Fast for Anyone to Use
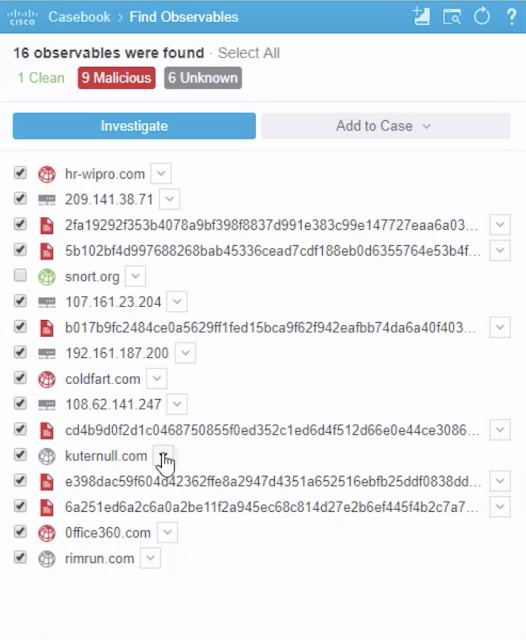
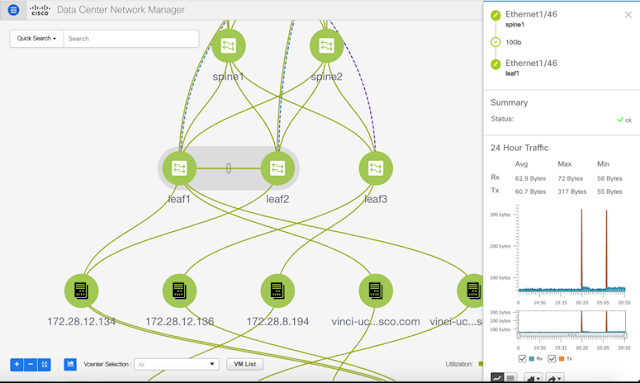
You don’t have to be an expert to use Cisco Threat Response. The interface is simple, intuitive, and interactive. Users can ask the tool to investigate a threat by simply cutting and pasting threat From the first click, Cisco Threat Response provides details on suspicious behaviors, files, and activities. Then click again, and it can be just as easy and quick to see, and in many cases remediate the root cause.
Easy-to-read, configurable graphics map the targets that have communicated with the malicious domain you’re investigating.
Not only that, information about the threat is collected and results are aggregated in the Cisco Threat Response portal. Here you get one common view, made even more powerful with knowledge from your other supported Cisco products. These products are fed by Talos, which delivers comprehensive threat intelligence with continuous updates to Cisco devices, automatically. In the Cisco Threat Response portal, it provides your network’s local sightings of the threat you’re investigating plus details to help you make timely and confident decisions about the best corrective actions.
Cisco Threat Response provides insights of integrated products to Investigate. The portal provides access to continuous threat intelligence geared to helping you respond quickly.
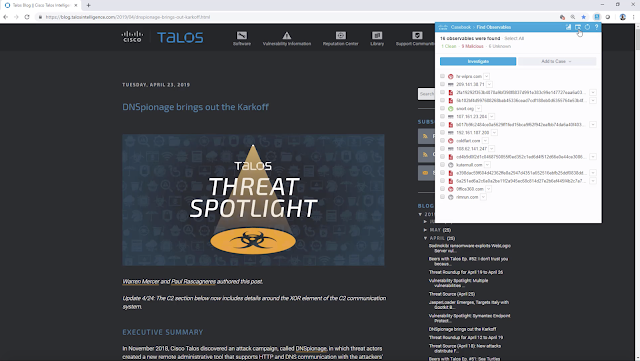
The browser plug-in makes it easy and convenient to pull indicators of compromise from any webpage or console and get verdicts directly from the drop-down. You can take corrective action or undertake a complete investigation (with collaboration and sharing) right from the page.
The More Cisco You Have, The More Value You Get
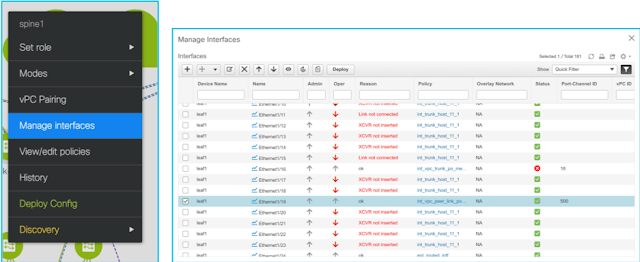
With the Firepower integration, Cisco Threat Response can now utilize intrusion alerts from the Firepower devices. This enrichment will amplify the contextual awareness in your network by harnessing the power of effective integrations with products such as AMP for Endpoints, Email Security, Threat Grid Umbrella and your Next-generation firewall. Another exciting thing about Cisco Threat Response is that when you have more Cisco solutions deployed, the integration drives more data enrichment and response capabilities. Contextual analysis becomes more detailed. We will continue to add new Cisco product integrations with Threat Response – the firewall products are only the most recent addition.