IT teams need agile delivery to keep pace with business demands. Today, enterprises are in the process of transitioning to a hybrid workforce, another rapid pivot that requires agile delivery. It’s essential to adapt to the new paradigm and in doing so, seek to minimize costs while still improving productivity, security, and the user experience. Cisco software platforms, like Cisco SD-WAN provide continuous value with new capabilities enabled in software.
Our latest Enterprise Networking release helps with this transition to hybrid work and provides value with innovations that provide greater integration that can reduce OpEx and CapEx spending and simplify operations. See the details below on new features in this release to help your IT team increase business agility and deliver more value for your organization.
First Cloud OnRamp for SaaS to optimize Webex experience
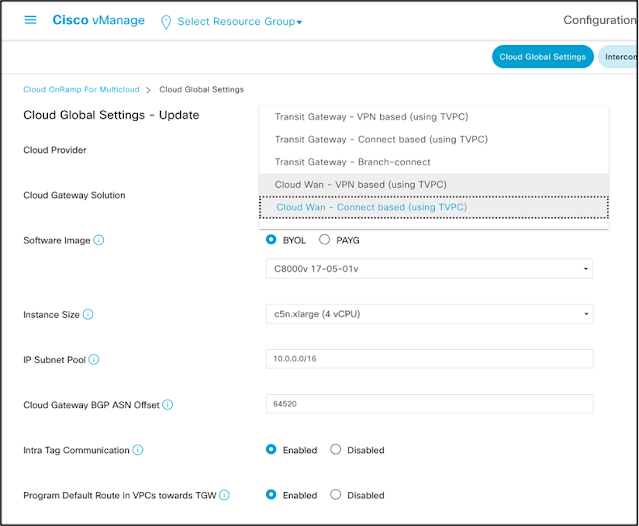
To improve and enhance the user experience for organizations, in our latest release (17.7) we are announcing Cisco SD-WAN Cloud OnRamp for SaaS integration with Webex. Cisco SD-WAN is the first solution to provide this level of integration and automation.
Cisco enables users to optimize Webex connectivity and performance when using Cisco SD-WAN. It does this by continuously monitoring all possible paths to Webex, and intelligently routing cloud application traffic to the best performing path, providing a fast, secure, and reliable end-user experience – and without human intervention.
The ultimate value for the users is that Cloud OnRamp for SaaS delivers path optimization and policy automation for Webex, so enterprises will be able to deliver a better application experience for their customers and employees.
Simplify CUBE functionality embedded in routers with Cisco SD-WAN
The new release enables native Cisco Unified Border Element (CUBE) support on Cisco enterprise routing platforms. CUBE is an enterprise-class Session Border Controller (SBC) performing critical voice routing, security, interworking and session management functions. Supported platforms include: ISR 4000, ISR 1100, and Catalyst 8200 as well as other ASR models.
The integration of this functionality into Cisco SD-WAN empowers customers to leverage the edge platforms to route collaboration application traffic between SD-WAN enabled nodes either within an enterprise (for on-prem deployments) or private / public cloud-based solutions. Customers can enable SBC functionality on their existing SD-WAN platforms allowing them to consolidate capabilities into a single platform, eliminating the need for an additional appliance. This integration reduces the number of platforms to purchase, license, power and manage; simplifies network architecture; and lowers costs and complexity.
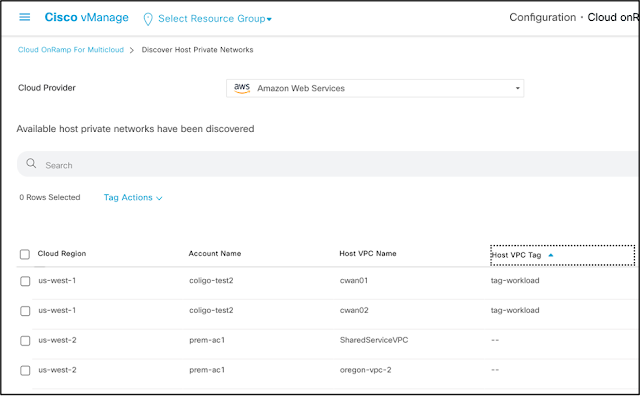
Ease operations with vManage Enhanced UX for Network Monitoring
Cisco is introducing enhanced vManage UX capabilities that enables IT managers and network operators to centrally automate the entire SD-WAN fabric, all in a highly visualized and intuitive user experience.
vManage is the single centralized dashboard for Cisco SD-WAN, addressing traditional challenges associated with device configuration, network management, and network monitoring with automation. It offers a highly visualized and intuitive user interface that simplifies and expedites network management and monitoring of SaaS, IaaS, and security for network operators.
vManage offers the following advantages:
◉ Intuitive user interface for easy consumption.
◉ Highly visualized network monitoring.
◉ Pre-configured templates automate and expedite the deployment of most common use cases.
◉ Guided step-by-step configuration designed to intelligently expedite onboarding of new devices.
◉ Expedite the Cisco ThousandEyes agent deployment for enhanced visibilities into internet, cloud, and SaaS
◉ Migrate to a SASE architecture with Cisco Umbrella
Greater reliability and resiliency with Cisco Integrated Services Router 1131
Cisco Integrated Services Router 1131 with WiFi-6 and 5G pluggable interface module
Cisco is introducing the next iteration of Cisco Integrated Service Router (ISR) optimized for cloud connectivity with built-in Wi-Fi 6 and pluggable 5G support for enhanced connectivity.
Built-in Wi-Fi 6 adds additional flexibility and scalability to existing networks, and pluggable 5G technology can provide greater reliability and resiliency. There is also support for full-stack security, including application aware firewall, IPS, URL-filtering, AMP, and Thread Grid.
SD-WAN has evolved beyond simply connecting users at the campus to applications in the datacenter. The value of network connectivity is the lifeblood of any enterprise today. The ability to connect users reliably and securely across multicloud, branch, datacenters, and hybrid workforce becomes a critical success factor to any organization.
Source: cisco.com