Saturday, 9 December 2023
How Cisco Black Belt Academy Learns from Our Learners
Wednesday, 6 December 2023
Why You Should Pass Cisco 350-701 SCOR Exam?
What Is the Cisco 350-701 SCOR Exam?
The 350-701 SCOR exam by Cisco assesses a wide range of competencies, encompassing network, cloud, and content security, as well as endpoint protection and detection. It also evaluates skills in ensuring secure network access, visibility, and enforcement.
The SCOR 350-701 exam, titled "Implementing and Operating Cisco Security Core Technologies v1.0," lasts for 120 minutes and includes 90-10 questions. It is linked to certifications such as CCNP Security, Cisco Certified Specialist - Security Core, and CCIE Security. The exam focuses on the following objectives:
Tips and Tricks to Pass the Cisco 350-701 SCOR Exam
When dealing with Cisco exams, it's essential to be clever and strategic. Here are some tips and techniques you can employ to excel in your Cisco 350-701 exam:
1. Have a Good Grasp of the Cisco 350-701 SCOR Exam Content
Initially, it's crucial to possess a well-defined understanding of the examination format. You must comprehend the expectations placed on you, enabling you to confidently provide the desired responses without hesitating among seemingly comparable choices.
2. Familiarize Yourself With the Exam Topics
Gaining insight into the goals of the Cisco SCOR 350-701 Exam can be highly advantageous. It allows you to identify the key concepts within the course, enabling a more concentrated effort to acquire expertise in those specific areas.
3. Develop a Study Schedule
Having a study schedule is crucial as it enhances organization and ensures comprehensive coverage. It provides a clear overview of the time available before the exam, allowing you to determine the necessary study and practice duration.
5. Perform Cisco 350-701 SCOR Practice Exams
Engaging in practice exams assists in identifying areas of deficiency, areas for improvement, and whether there's a need to enhance speed. You can access dependable Cisco 350-701 SCOR practice exams on the nwexam website. Repeat the practice sessions, pinpoint your weaker areas, monitor your results, and ultimately build confidence in your knowledge and skills.
6. Engage in Online Forums
Numerous online communities are specifically focused on Cisco certifications and exams. By becoming a part of these communities, you can connect with individuals possessing relevant experience or working as professionals in the field. Their insights and recommendations will assist you in steering clear of errors and optimizing your work efficiency.
7. Brush Up on Your Knowledge Right Before the Exam
Having a concise set of notes that you can review just before the exam is beneficial. This aids in activating your memory and bringing essential knowledge to the forefront of your mind, saving valuable time that might otherwise be spent trying to recall information.
8. Strategies for Multiple-Choice Questions
Utilizing Multiple-Choice Questions strategies is beneficial when you're uncertain about the correct answer. For instance, employing the method of eliminating incorrect options can be effective. It's also advisable to skip questions that are challenging, proceeding to the others without spending excessive time on them. Complete the remaining Cisco 350-701 questions and return to the challenging one later.
Why Should You Pass the Cisco 350-701 SCOR Exam?
Indeed, examinations are commonly undertaken to acquire the knowledge and skills necessary to address human challenges. Successfully completing the Cisco 350-701 SCOR exam offers more than just that – it grants the CCNP Security certification and additional advantages, including:
1. Set Yourself Apart From the Crowd
The job landscape for IT professionals is intensely competitive. Simultaneously, hiring managers are compelled to seek exceptionally skilled candidates. Consequently, only individuals who have demonstrated dedication and commitment to their careers through examinations and certifications are chosen. Opting for a Cisco 350-701 SCOR exam also signifies your enthusiasm and practical expertise in your professional domain.
2. Official Validation
Consider the perspective of the hiring manager: asserting your proficiency in network security technologies through words alone may not be highly persuasive. However, when your resume is enhanced by an industry-standard certification from a reputable vendor, additional explanations become unnecessary. The esteemed reputation of Cisco in the networking field alone is sufficient to secure a job.
3. Showcase Your Professional Relevance
Many employers prefer to recruit versatile professionals capable of undertaking diverse responsibilities within a company. Successfully completing the Cisco 350-701 SCOR exam demonstrates your accurate understanding of workplace technologies and your capacity to contribute to organizational empowerment. In essence, certification assures your employer that your skill set aligns with the requirements of their job position.
4. Boost Your Earnings
Attaining the CCNP Security certification opens doors to lucrative opportunities for increased earnings. Additionally, you become eligible for job positions that offer higher salaries compared to those available to non-certified professionals.
5. Propel Your Career Advancement Swiftly
If you've been aiming for promotions within your company, obtaining CCNP Security certification can be instrumental in reaching even managerial positions. The widespread application of Routing and Switching technologies in many organizations is attributed to their provision of secure communication and data sharing.
6. Reinforce Your Confidence
Positions in networking are typically hands-on, demanding consistent performance. Successfully completing the Cisco 350-701 SCOR exam instills confidence in executing tasks, as the acquired skills provide a robust comprehension of network security. Certifications also hold significance for employers during the hiring process, serving as proof that they have selected a qualified and capable professional.
Conclusion
Ascending to higher levels and achieving your aspirations in the IT field can be challenging without additional certifications validating your capabilities. Although various organizations provide numerous certifications, it's crucial to identify the one that aligns most effectively with your objectives. Otherwise, the investment of time and money could prove futile. Act promptly and secure your Cisco 350-701 SCOR certification using the best available resources tailored for you.
Tuesday, 5 December 2023
Integrated Industrial Edge Compute
Industry Trends
Container Apps at the Cisco Edge
And More
Saturday, 2 December 2023
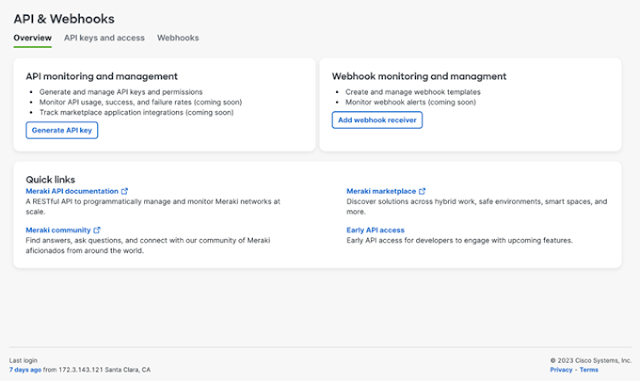
Effortless API Management: Exploring Meraki’s New Dashboard Page for Developers
A Dashboard Designed for Developers
Simplifying API Key Management
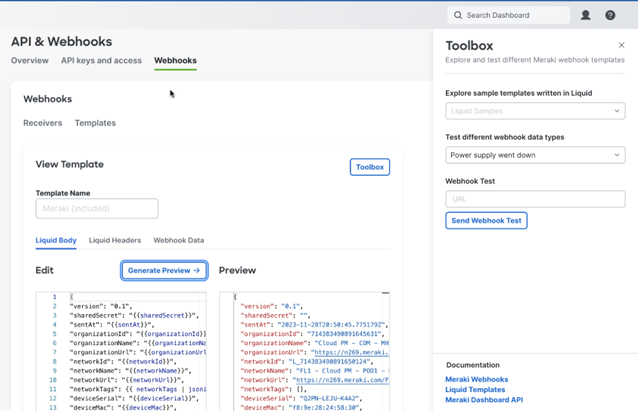
Streamlining Webhook Setup
- Create webhook receivers across your various networks
- Assign payload templates to integrate with your webhook receiver
- Create a custom template in the payload template editor and test your configured webhooks.
- Establish custom headers to enable adaptable security options.
- Experiment with different data types, like scenarios involving an access point going offline or a camera detecting motion, for testing purposes.
Access to Essential Documentation and Community Resources
What’s on the Horizon?
Thursday, 30 November 2023
Making Your First Terraform File Doesn’t Have to Be Scary
The HCL File: What Terraform will configure
The Terraform workflow: How Terraform applies configuration
A bonus tip
Saturday, 25 November 2023
10 Useful Tips to Ace Cisco 300-415 ENSDWI Exam
Decoding 300-415 ENSDWI Exam
The 300-415 ENSDWI exam delves into Implementing Cisco SD-WAN Solutions, evaluating candidates' proficiency in orchestrating WAN edge routers to connect to the SD-WAN fabric. This exam is not merely a test of theoretical knowledge but a practical assessment of your ability to deploy, manage, and troubleshoot SD-WAN solutions in real-world scenarios.
Before delving into preparation tips, it's crucial to understand the terrain you'll be navigating. The 300-415 ENSDWI exam typically consists of 55-65 questions; candidates are allotted 90 minutes for completion. The format encompasses a variety of question types, including multiple-choice, drag-and-drop, and simulation-based scenarios.
Cisco 300-415 ENSDWI Exam Objectives
Ten Expert Tips for 300-415 ENSDWI Preparation
1. Create a Study Plan
Building a structured study plan is the foundation of successful exam preparation. Allocate dedicated time daily to cover specific topics, ensuring a balanced approach to all exam objectives. Consistency is key, and a well-organized study plan will help you stay on track.
2. Hands-On Practice
Theory is vital, but practical application is paramount. Set up a virtual lab environment to experiment with SD-WAN configurations. The hands-on experience will reinforce theoretical concepts and enhance your troubleshooting skills—a crucial aspect of the exam.
3. Utilize Official Cisco Resources
Cisco provides many official resources, including documentation, whitepapers, and video tutorials. These materials offer insights into SD-WAN technologies and Cisco's expectations for exam candidates. Leverage these resources to complement your study materials.
4. Join Online Communities
Engage with fellow candidates and networking professionals in online forums and communities. Discussing concepts, sharing experiences, and seeking clarification on doubts can provide a fresh perspective and fill gaps in your understanding. The collective wisdom of the community is a valuable asset.
5. Use Cisco 300-415 ENSDWI Practice Test
Perform Cisco 300-415 ENSDWI practice tests to familiarize yourself with the time constraints and pressure. Timed practice exams assess your knowledge and train you to manage time effectively during the test. This step is crucial for building confidence and reducing exam-day anxiety.
6. Focus on Weak Cisco 300-415 ENSDWI Syllabus Topics
Regularly evaluate your progress and identify weak areas. Allocate additional time to reinforce your understanding of these topics. Whether it's troubleshooting, security configurations, or SD-WAN policies, addressing weaknesses proactively will contribute to a more well-rounded preparation.
7. Stay Updated with Industry Trends
The world of networking is dynamic, with technologies evolving rapidly. Stay abreast of industry trends, especially those related to SD-WAN. Familiarizing yourself with the latest developments ensures that your knowledge is exam-centric and reflective of real-world scenarios.
8. Explore Third-Party Study Materials
While official Cisco resources are indispensable, exploring third-party study materials can offer diverse perspectives. Books, practice exams, and online courses from reputable sources can provide alternative explanations and additional context, enriching your understanding.
9. Teach to Learn
The act of teaching reinforces your understanding. Collaborate with study partners or create study guides for specific topics. Explaining concepts in your own words solidifies your knowledge and highlights areas in which you need further clarification.
10. Review and Revise Cisco 300-415 ENSDWI Exam Topics
Continuous revision is the key to retention. Periodically revisit previously covered topics to reinforce your memory. The spaced repetition technique, where you review information at increasing intervals, is particularly effective in ingraining knowledge for the long term.
Beyond 300-415 Exam: The CCNP Enterprise Certification
Earning the 300-415 ENSDWI certification is a significant accomplishment, but it's just one piece of the puzzle. Combining it with the 350-401 ENCOR (Implementing and Operating Cisco Enterprise Network Core Technologies) exam leads to the coveted CCNP Enterprise certification.
1: Career Paths with CCNP Enterprise
The CCNP Enterprise certification opens doors to a myriad of career opportunities. You become a sought-after professional capable of designing and implementing complex enterprise network solutions. Roles such as Network Engineer, Systems Engineer, and Network Administrator are within reach.
2: Industry Recognition
CCNP Enterprise certification is globally recognized and respected. It serves as a testament to your expertise in networking technologies and positions you as a qualified professional in the eyes of employers worldwide. This recognition can be a game-changer in job interviews and salary negotiations.
3: Salary Advancement
With CCNP Enterprise certification, you're not just acquiring knowledge but investing in your earning potential. Certified professionals often command higher salaries than their non-certified counterparts. The certificate becomes a tangible asset, showcasing your dedication to continuous learning and mastery of your craft.
Conclusion
The journey to mastering the 300-415 ENSDWI exam is undoubtedly challenging, but the rewards are commensurate with the effort invested. As you delve into the intricacies of SD-WAN solutions, remember that each concept mastered is a step closer to unlocking a world of career possibilities. The CCNP Enterprise certification, born from the synergy of 300-415 ENSDWI and 350-401 ENCOR, is your passport to a future where your expertise is valued and indispensable in the ever-evolving networking landscape. So, gear up, embrace the challenge, and set forth on the path to CCNP Enterprise mastery. Success awaits those who dare to venture into the realm of possibilities that certification unlocks.
Thursday, 23 November 2023
Secure Multicloud Infrastructure with Cisco Multicloud Defense
It’s a multicloud world!
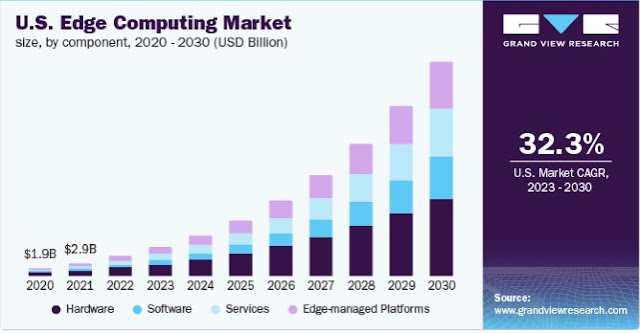
Market Trend
- Security: Provides a full suite of security capabilities for workload protection
- Cloud: Integrates with cloud constructs, enabling auto-scale and agility
- Networking: Seamlessly and accurately inserts scalable security across clouds without manual intervention
- Keep policies up to date in near-real time as your environment changes.
- Connect continuous visibility and control to discover new cloud assets and changes, associate tag-based business context, and automatically apply the appropriate policy to ensure security compliance.
- Power and protect your cloud infrastructure with security that runs in the background via automation, getting out of the way of your cloud teams.
- Mitigate security gaps and ensure your organization stays secure and resilient.
Cisco Multicloud Defense Overview
- Multicloud Defense Controller (Software-as-a-Service): The Multicloud Defense Controller is a highly reliable and scalable centralized controller (control plane) that automates, orchestrates, and secures multicloud infrastructure. It runs as a Software-as-a-Service (SaaS) and is fully managed by Cisco. Customers can access a web portal to utilize the Multicloud Defense Controller, or they may choose to use Terraform to instantiate security into the DevOps/DevSecOps processes.
- Multicloud Defense Gateway (Platform-as-a-Service): The Multicloud Defense Gateway is an auto-scaling fleet of security software with a patented flexible, single-pass pipelined architecture. These gateways are deployed as Platform-as-a-Service (PaaS) into the customer’s public cloud account(s) by the Multicloud Defense Controller, providing advanced, inline security protections to defend against external attacks, block egress data exfiltration, and prevent the lateral movement of attacks.
Multicloud Defense Gateways
- High throughput and low latency
- Reverse proxy, forward proxy, and forwarding mode
- Flexibility in selecting relevant advanced network security inspection engines, including TLS decryption and re-encryption, WAF (HTTPS and web sockets), IDS/IPS, antivirus/anti-malware, FQDN and URL filtering, DLP
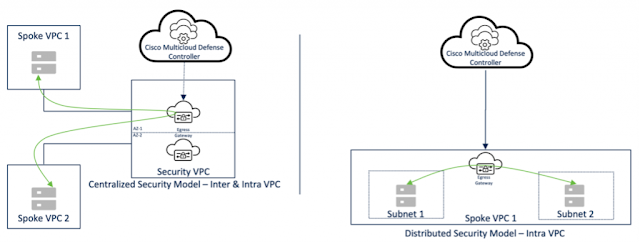
Security Models
- For scalability, autoscaling is supported.
- For resiliency, auto-scaled instances are deployed in multi-availability zones.
- For scalability, autoscaling is supported.
- For resiliency, auto-scaled instances are deployed in multi-availability zones.
- For scalability, autoscaling is supported.
- For resiliency, auto-scaled instances are deployed in multi-availability zones.
Use-cases
- In the centralized security model, traffic is inspected by gateways deployed in the security VPC/VNet/VCN.
- Gateways are auto-scale and multi-AZ aware.
- In the distributed security model, traffic is inspected by gateways deployed in the application VPC/VNet/VCN.
- In the centralized security model, traffic is inspected by gateways deployed in the security VPC/VNet/VCN.
- In the distributed security model, traffic is inspected by gateways deployed in the application VPC/VNet/VCN.
- Gateways are auto-scale and multi-AZ aware.
- In the centralized security model, intra and inter-VPC/VNet/VCN traffic is inspected by gateways deployed in the security VPC/VNet/VCN.
- In the distributed security model, intra-VPC/VNet/VCN traffic is inspected by gateways deployed in the application VPC/VNet/VCN.
- Gateways are auto-scale and multi-AZ aware.
- URL filtering requires TLS decryption on the gateway.
- FQDN-based filtering can be enforced on encrypted traffic flows.