Isn’t it great when the enterprise technology solutions you use to achieve various business outcomes partner and work seamlessly with each other? Cisco and Microsoft have done just that to provide you with a scalable and high-performance cloud infrastructure along with easy and effective cloud security.
In 10 minutes or less, Cisco Stealthwatch Cloud extends visibility, threat detection, and compliance verification to Microsoft Azure without agents or additional sensor deployments within your cloud environment.
Enterprises are continuously adopting the public cloud for many reasons, whether it’s greater scalability, better access to resources, cost savings, increased efficiency, faster time to market, or overall higher performance. While the move to the cloud offers great opportunities, it also means that the old ways of thinking about security aren’t working for most organizations anymore, especially when it comes to visibility in the cloud.
In 10 minutes or less, Cisco Stealthwatch Cloud extends visibility, threat detection, and compliance verification to Microsoft Azure without agents or additional sensor deployments within your cloud environment.
A new way to think about security
Enterprises are continuously adopting the public cloud for many reasons, whether it’s greater scalability, better access to resources, cost savings, increased efficiency, faster time to market, or overall higher performance. While the move to the cloud offers great opportunities, it also means that the old ways of thinking about security aren’t working for most organizations anymore, especially when it comes to visibility in the cloud.
Often this lack of visibility leads to challenges surrounding network traffic analysis, identity and access management, compliance and regulation, and threat investigation. We all know of organizations that have made security mistakes related to configuration and inadvertently exposed their private data, resulting in serious repercussions. Of course, training can be improved, configurations checked, and automated tools used to validate configuration parameters, but these efforts only address the preventative aspects of security practice. Organizations also need to actively watch what is actually happening with their cloud assets and catch the threats that aren’t prevented. Active breach detection starts with improved visibility. Complete visibility gives you a way to protect your cloud infrastructure in real-time, so you can be agile and address issues as they arrive.
Cloud security: a shared responsibility
While your cloud provider manages security of the cloud, security in the cloud is the responsibility of the customer. You as a customer retain control of what security you choose to implement in the cloud to protect your content, platform, applications, systems and networks, no differently than you would in your company’s private datacenter.
How do you know what is happening to data in the cloud? How do you know you’ve configured your cloud assets to be secure? How do you recognize cloud assets starting to communicate with new, possibly hostile internet sites? How do you do it in real time and quickly enough to mitigate data loss?
To answer these questions, it’s critical to have an active breach detection solution for your public cloud. And for that solution to be effective, the cloud provider needs to enable the right visibility to tap into valuable cloud network and configuration telemetry.
Cisco and Microsoft: better together
In the continuous effort to provide customers with industry leading solutions, Cisco has been working with Microsoft to bring Cisco Steathwatch Cloud to Azure. Stealthwatch Cloud, a software as a service (SaaS) active breach detection solution based on security analytics, can now deliver comprehensive visibility, and effective threat detection in Azure environments in as little as 10 minutes.
Traditionally, organizations have tried to overlay a patchwork of agents across cloud assets to detect bad activity. This approach requires significant costs and effort to deploy, maintain, and manage in dynamic environments such as the cloud. Importantly, it frequently doesn’t scale with your cloud environment with regard to cost. But Stealthwatch Cloud can deploy within your Azure environment with no need for an agent and scales up and down according to your actual cloud traffic utilization.
How does it work?
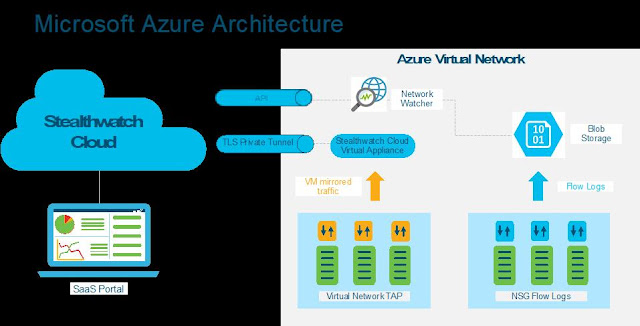
Microsoft provides Azure Network Security Group (NSG) flow logs that contain valuable information on north-south and east-west traffic within an Azure virtual network. Flow logs show outbound and inbound flows on a per flow basis, the network interface (NIC) the flow applies to, 5-tuple information about the flow (Source/destination IP, source/destination port, and protocol), if the traffic was allowed or denied, and in Version 2, throughput information (Bytes and Packets, and the NSG rule applied to the traffic). Organizations use this information to audit activity on their cloud network. Stealthwatch Cloud can natively consume NSG flow logs V2 via APIs, without having to deploy any agents or sensors.
Additionally, Microsoft has also introduced Azure virtual network TAP (Terminal Access Point) that allows you to continuously and easily stream your virtual machine network traffic to Stealthwatch Cloud like a traditional, physical network SPAN or TAP. You can add a TAP configuration on a network interface that is attached to a virtual machine deployed in your virtual network. The destination is a virtual network IP address in the same virtual network as the monitored network interface or a peered virtual network. This approach provides access to not just flow logs, but also other network traffic like DNS data.
Stealthwatch Cloud can be powered by both NSG flow logs v2 and vTAP data. Stealthwatch Cloud analyzes this data using entity modeling to identify suspicious and malicious activity. For every active entity on the network, Stealthwatch Cloud builds a behavioral model – a simulation of sorts – to understand what the entity’s role is, how it normally behaves, and what resources it normally communicates with. Then it uses this model to identify changes in behavior consistent with misuse, malware, compromise, or other threats.
For instance, if an Azure resource normally only communicates with internal hosts, but suddenly it begins sending large amounts of data to an unknown external server, it could be a sign of data exfiltration. Stealthwatch Cloud would detect this behavior in real-time and alert your security team.