Cisco Threat Response: For security analysts, by one of their own
The work of a security analyst is arduous and time consuming but rewarding too. I know, I spent a good part of my career sitting in a seat, investigating and responding to threats in a Security Operations Center (SOC). I spent way too many hours and weekends moving from console to console piecing together information from disparate systems to investigate a single threat. The various SOCs I was part of were made up of millions of dollars in the latest, best-of-breed technologies alongside open source components and scripts that were supposed to work together but too often didn’t.
That’s why I’ve been focused on designing and building systems to make the lives of the security analyst easier and their work more effective. It’s rewarding to see the products we’ve built have a positive impact on an analyst’s abilty to do their job effectively. A year ago, we introduced a new application for security analysts to make security investigations fast and easy. It pulls content for detection and response from across the security stack: from the cloud, network, endpoint together in a central location. We call it Cisco Threat Response.
Rapid Adoption
Since we released the first version of Threat Response a year ago, it has been used in more than 3,600 SOCs, and has even added value in organizations without full blown SOCs. The feedback has been incredible and has given us so much confidence in Cisco Threat Response, we’re giving it away at no cost to existing customers. It’s included with the license for any Cisco Security product that integrates with it. As good as our Cisco Security products perform on their own, we know that they are even more effective when they’re used together. It’s all about making your SOC operations run faster: from detection, through investigation, to remediation. How? It’s all API-driven.
API-Driven
Cisco Security products have used APIs for years. The difference now is that Cisco Threat Response pulls them together so you don’t have to. With long lists of observables to investigate, Threat Response gets you immediate answers by calling both threat intelligence and our security portfolio APIs — confirming threats and showing you exactly where you’re affected — delivering a clear view of what’s happening.
Customers are excited to learn they can also utilize these APIs to integrate Threat Response directly into their existing Security Incident and Event Management systems (SIEMs) and Security Orchestration, Automation, and Response tools (SOARs). Customers even report they see Threat Response reducing the burden on their SIEMs.
And our customers seem to love this approach. One customer wrote to us “I like quickly being able to see infections on my network and this presents them in a really nice fashion…” Another said, “You cannot hit a target you cannot see. Threat Response simplifies security analysis”
Security integrations that simplify SOC operations
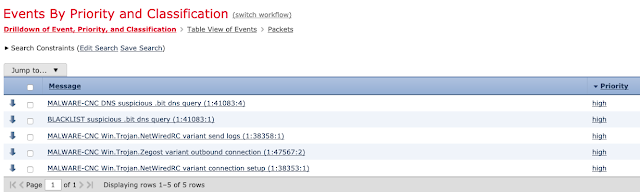
Picture a typical investigation that happens many times a day in SOCs around the world: A potential Emotet malware outbreak. Maybe you’ve investigated it yourself. Emotet a well-known banking trojan that attackers love, keeps coming back in fresh, new forms. The Indicators of Compromise associated with it include a very, very long list of known file hashes, distribution domains, and command-and-control IP Addresses. Investigating these observables one at a time to see if you’re affected can take hours.
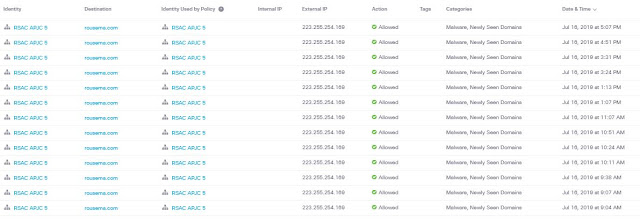
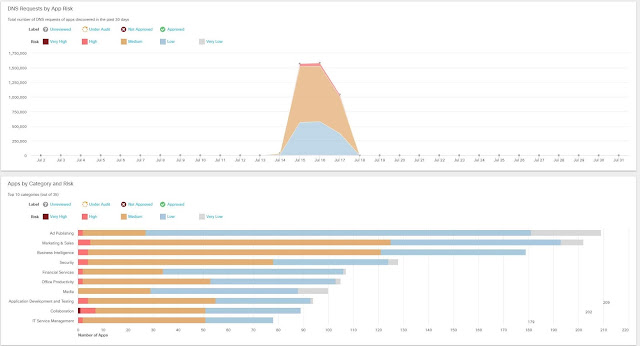
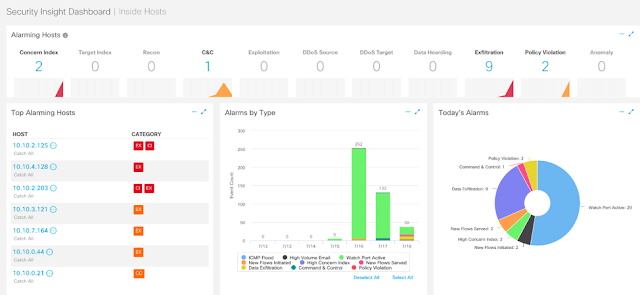
Cisco Threat Response calls threat intelligence APIs to gather the all the dispositions for each one at once. Then it calls the Cisco Security products’ APIs and learns what each one knows about every observable. Cisco AMP for Endpoints knows what systems have the malicious file hashes. Cisco Umbrella knows which devices called out to malicious domains. Integrating your Email Security Appliance (ESA) lets you know who received that attachment or phishing URL and so forth until it gathers everything necessary to show you exactly what is happening in your environment.
More than a Pretty Face
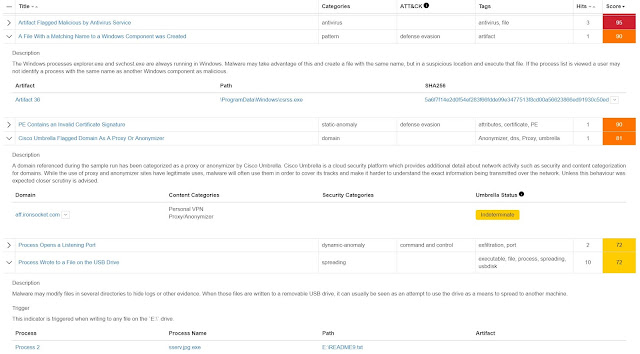
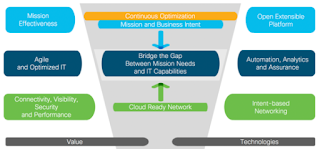
Threat Response reflects years of back-end integration work by engineering. It begins and ends with a highly integrated architecture of world-class threat intelligence coupled the integration of advanced security technologies covering the attack surface across the cloud, network and endpoint. This is critical for effective, consistent detection and response across the critical points of your architecture.
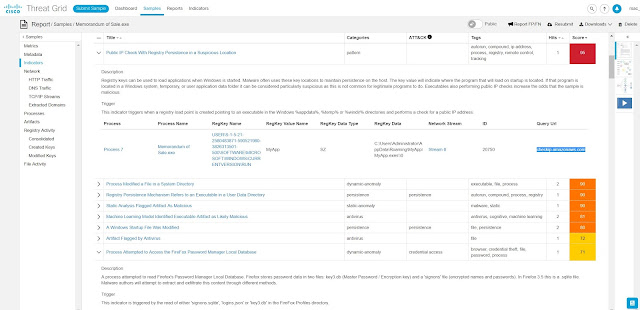
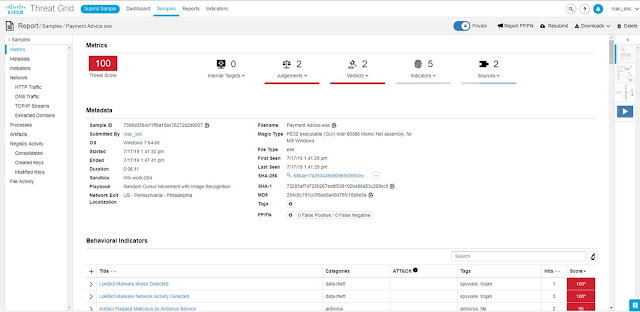
Borrowing from the earlier example, an unknown file in an Emotet variant gets analyzed by our Threat Grid Malware Analysis engine and finds malicious behavior. Our architecture allows Threat Grid to share this intelligence across the entire portfolio so this file is blocked at the endpoint, in email, on the network for every customer around the world in a matter of minutes. And Threat Response shows you exactly every place where you were targeted by that file and confirms where it was blocked or detected.
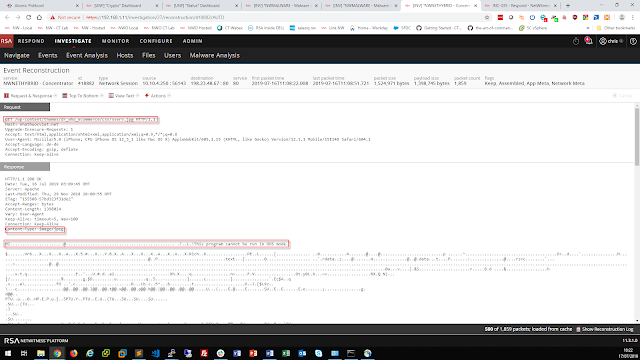
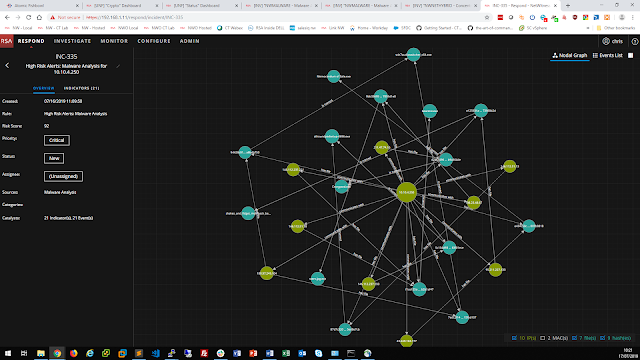
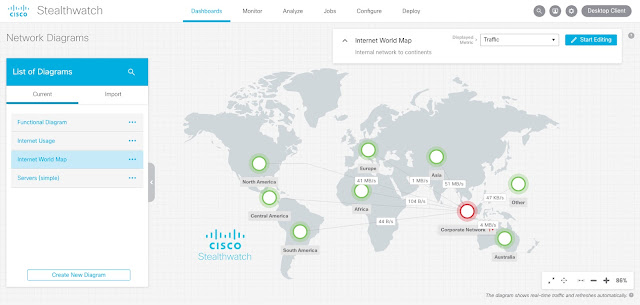
Getting the Full Picture – the Relations Graph
That clear view we provide is perhaps the most compelling technology in Cisco Threat Response. By visually depicting the relationships among the observables and dispositions, the affected systems in your environment (called Targets and shown in purple), and the other systems that are related to the outbreak, you’ll know immediately whether you’re affected and how. Skip the hours and hours of investigation time.
Plus, you can take action directly from the Relations Graph. It provides actions (called Pivot Menus) from which you can continue the investigation in the other products’ consoles (taking you there seamlessly) or call their APIs directly to take action. Those Targets shown in purple? Maybe you want to quarantine those hosts through AMP for Endpoints, which you can do with a single click. Those malicious C2 domains? Maybe you want to tell Umbrella to block, at the DNS layer, everything on your network from connecting to them, which you can with another click.
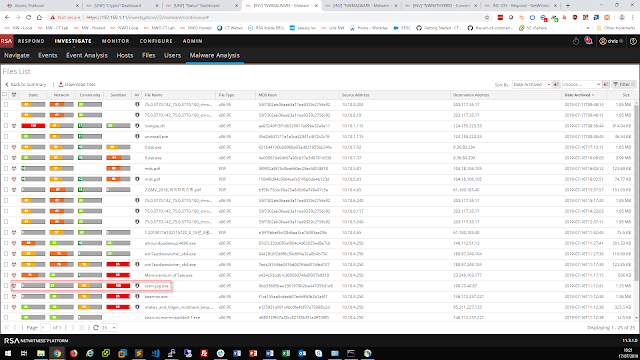
Sources of Detection
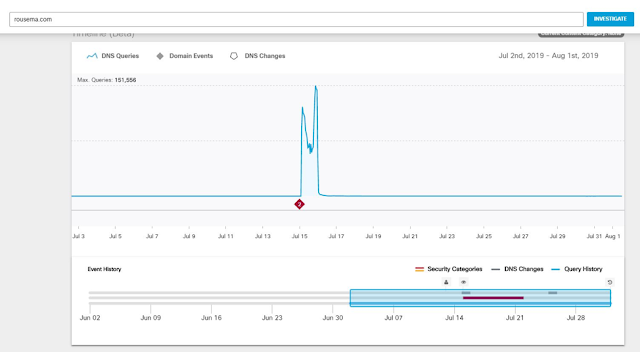
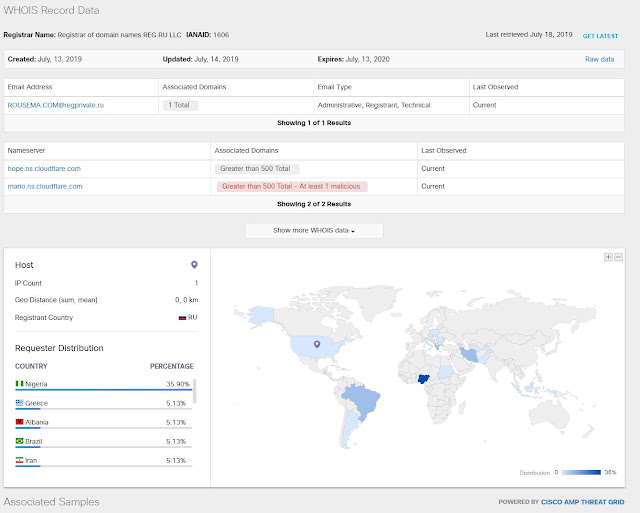
Threat Response is driven by the individual Cisco Security products and threat intelligence sources that feed into it. Cisco Talos research and Threat Grid for threat intelligence, Threat Grid for static and dynamic file analysis, AMP for Endpoints for dynamic and retrospective endpoint detection and response, Email Security (the number one vector of attack), Umbrella for internet domain intelligence and blocking, and Next Generation Firewall for network detection and blocking. Threat Response brings these products together to bring you context about the events seen in your environment allowing you to further enrich this context with your own intelligence sources.
Operationalizing Threat Intelligence
One of the most popular features is the browser plug in we’ve developed that takes unstructured data from any webpage or application, finds the observables or indicators of compromise and automatically renders a verdict on that observable (clean, malicious, unknown) based on our threat intelligence. Like that Talos blog example we used earlier: one click pulls all the observables mentioned on that page without the need to manually cut and paste each one (and there are 634 observables mentioned – I had them counted!) Moreover, you can access the Threat Response pivot menu, including domain blocking, without ever leaving the page.
The best part about Threat Response is rate of innovation within the application. The endgame is better cybersecurity through better SOC operations: faster detections, simpler investigations, and immediate responses. We love what we have released to date and even more excited about our roadmap. Our engineering teams are delivering new enhancements, including new features and product integrations every two weeks. There’s much more to say about Threat Response than I can detail in a blog. I encourage you to experience it for yourself. The work of the SOC teams is too important to be tedious and increasing their efficiency will have better security outcomes for everyone.