In the last year, communication networks have emerged as a de facto way for people to stay connected with their family and friends and carry out their professional tasks, as lockdowns and social distancing norms made it impossible to lead normal lives. Telco network became the digital foundation for everything that needed connection for instance eEducation, eHealth, eCommerce, eRetail, etc. However, while people in urban areas have used high-speed broadband and digital platforms to stay connected during these unprecedented times, this is hardly true for rural and remote areas.
While the number of internet users continues to grow, 51% of the world’s population is still not using mobile internet, as per a recent GSMA report. It further says that if the current trends continue, more than 40% of the population in low- and middle-income countries will remain offline in 2025.
The fact is that it is incredibly challenging for the service providers to provide connectivity in rural areas. The high cost of setting up and managing the network coupled with low returns of investment spread over an extended period of time is the key reason for the service providers’ reluctance to set up communications networks in rural and remote areas. In addition, low population density and challenging terrain further add to the challenge.
There is a growing realization among the service providers that the network strategy for the urban markets is not suitable for the remote and rural areas. It is then a moral dilemma for the telcos.
Innovating To Provide Connectivity In Rural Areas
There is a need to innovate and go beyond the traditional network deployment models to provide high-speed broadband connectivity in rural and difficult-to-reach areas.
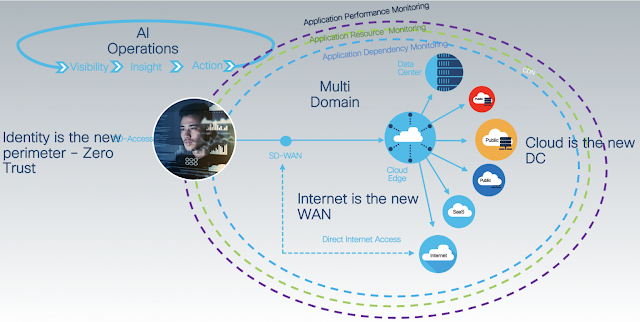
The telco’s need to relook and reimagine their current network architecture, which is very complex. The conventional network strategy of adding a layer for every new standard is adding to the complexity. Further, the data centers are monolithic, making it challenging for the telco’s to capture the monetization opportunity that is emerging at the edge of the network while they are connecting everything e.g. devices, machines, industries, meters, security cameras, etc, etc., everything that is benefiting from a digital connection.
Moving from monolithic, hardware-centric networks to software and an open network infrastructure can bring down cost and enable telco’s to provide connectivity in remote areas without compromising profitability. In other words, network economics need to change to adapt to this dynamic market opportunity and need.
Open Radio Access Networks (RAN)
Several new-age innovations, including Open Radio Access Networks (RAN), Edge computing and cloud-native architecture, AI/ML, etc. promise to change this and provide high-speed and reliable connectivity at a cost that is viable for unconnected and in far flung / remote areas.
Open RAN specifically is the game-changer. Essentially, it disaggregates the software and hardware components of the network infrastructure, making it easier and more economically viable to provide internet in remote areas. In addition, the disaggregation of the RAN functions helps in bringing down network cost and complexity. Further, Open RAN deployments do away with vendor lock-in and allow service providers to benefit from virtualization.
The expenditure on RAN accounts for a significant chunk of telco’s capital expenditure. With Open RAN, they are able to bring down the cost by leveraging the open ecosystem and cloud economics. Mobile operators operate in an intensely competitive environment and are constantly stressed to increase capacity and reduce costs. The Open RAN approach allows them to address these issues, and the improved cost economics makes it easier to connect the unconnected and bridge the digital divide.
Cloud-native Mobile Networks
The success of Japan’s Rakuten Mobile, a greenfield operator, is showing us the way. It operates the world’s first fully cloud-native mobile network. Rakuten Mobile launched 4G service in April 2020 and followed this by launching 5G Non-Standalone within few months in September 2020. A cloud-native and automated network promises to bring the benefits of connectivity in yet-to-be-connected areas, thus transforming lives and powering economies.
The industry needs a paradigm shift in thinking beyond the traditional network deployment approach to connect the remaining half of the world’s population. Telco’s need to experiment with out-of-the-box solutions to bridge the digital divide. This will not only allow them to add new subscribers to the network but also contribute to the overall economic and social growth.
Source: cisco.com